- Vulnerable U
- Posts
- Iranian Attackers Retaliate With Stryker Attack and Much More
Iranian Attackers Retaliate With Stryker Attack and Much More

Iranian-linked hacktivists are claiming responsibility for a destructive attack against medical device giant Stryker, and the details coming out are nuts.
From everything we’ve seen so far, this looks like a straight-up wipe: systems reset, servers knocked offline, login pages defaced, and employee devices, including some personal phones enrolled for work access, apparently wiped after attackers gained deep administrative control.
The group claiming responsibility, Handala, framed the operation as retaliation for the US-Israeli war on Iran, including the bombing of an all-girls school.
Meanwhile, researchers are documenting Iranian-linked actors scanning exposed surveillance cameras in missile-hit regions to support battle-damage assessment, while Iranian state-linked channels are openly circulating Telegram target lists naming cloud, AI, and R&D facilities belonging to Amazon, Microsoft, Google, IBM, Nvidia, Oracle, and Palantir.
Rapid7 also warned that Iranian groups like APT35, APT42, MuddyWater, and OilRig remain highly relevant in the current environment, with phishing, credential abuse, and reconnaissance likely to intensify.
Targets Chosen for Widest-Possible Blast Radius
If you’re not in healthcare, you might not know the name immediately. I actually didn’t. But once this story started moving, it became very obvious that this is not some niche company nobody relies on. Stryker is a major medical device maker with roughly 56,000 employees, and it builds everything from surgical and imaging equipment to hospital beds, defibrillators, and systems used by the U.S. military.
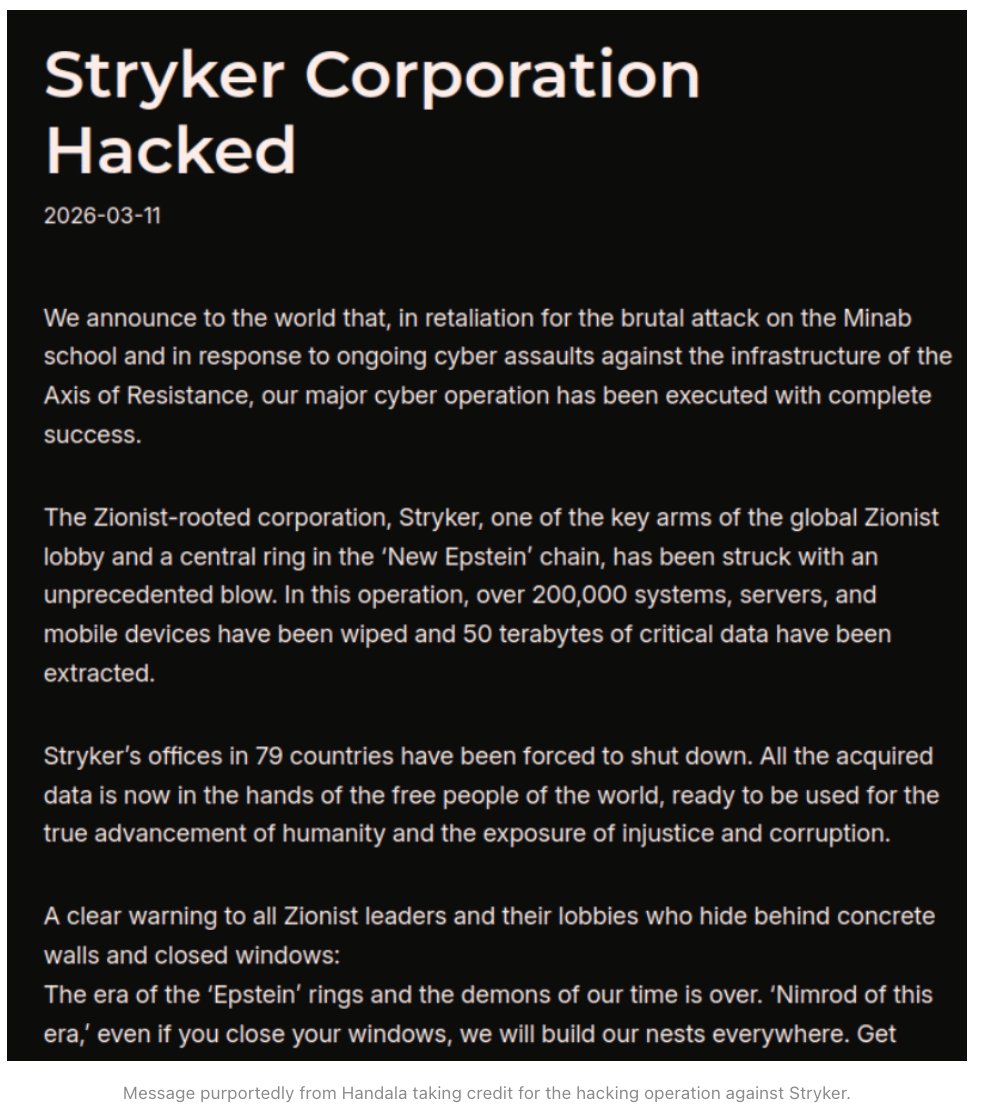
Iranian-linked hacktivists from a group called Handala are claiming they hit Stryker, and the description coming out of this incident is about as destructive as it gets. Kim Zetter reported that Stryker employees in the U.S., Australia, India, Ireland, and elsewhere began posting that the company had effectively gone hard down. Internal and admin pages were reportedly defaced with Handala branding, the group claimed it hit more than 200,000 systems and devices, and Stryker itself told employees it was dealing with a “severe, global disruption” affecting laptops and systems connected to its network.
The way people were describing it, this wasn’t just “we can’t log into one app” or “VPN is down.” Employees were saying systems were reset, servers were inaccessible, and the whole company was at a standstill.
A Reddit post said three Stryker-managed devices were wiped around 3:30 a.m. EDT and that the Entra login page had been defaced with the Handala logo. Zetter also reported employee accounts saying attackers pushed OS resets to computers and phones connected to the company network and that many servers were wiped clean.
The Intune angle makes this especially nasty.
From the employee accounts that surfaced, it sounds like one of the hardest-hit areas involved personal phones enrolled for work access — the classic BYOD trap. A company says, “Sure, use your own phone for work, just install our MDM software and we’ll only touch the corporate stuff.” But that’s policy, not technical reality. If attackers get access to your Intune admin layer, they don’t have to honor the company’s policy. They can use the same device-management power to wipe enrolled devices, cut off access, and break whatever authentication chain those phones were part of.
Employee posts cited by Zetter said colleagues were told to remove Intune, Company Portal, Teams, and VPN from personal devices, and some users said they lost all personal data and could no longer access email or MFA-protected accounts.
That’s the part that should make every company doing BYOD stop and think for a minute. Once the attackers have that level of administrative access, they don’t just have the ability to wipe. They may have had the ability to read, export, or collect data too.
Handala has a history of stealing and publishing sensitive data, and The Register noted that the group or Iran-linked channels are now threatening a wider set of U.S.-linked technology targets as the conflict expands. So if they wiped Stryker, the obvious question is whether they also took a copy of what they wanted first. At this stage, there’s no public proof either way. But if you know the playbook, it’s hard not to ask.
The company’s official language is what you’d expect early in an incident.
Stryker said it was experiencing a global network disruption affecting its Windows environment and that teams were working to restore operations. That’s standard, cautious wording. But it doesn’t change what the early employee reports and the public claim of responsibility suggest: this was not a normal outage and not a normal breach. If the wipe reports are accurate, this was a destructive cyberattack in every sense of the word.
Iran Weaponizes the Cameras
According to Zetter, the group said the attack was partly retaliation for the U.S. bombing of an all-girls school in Iran on the first day of the U.S.-Israeli assault. Whether you take every element of the group’s narrative at face value or not, they are clearly framing this as geopolitical retaliation, not crime for profit. That’s why I don’t think this story should be viewed in isolation.
This morning I was also looking at Check Point’s new research showing Iranian-linked actors scanning the internet for exposed Hikvision and Dahua cameras across Israel, Qatar, Bahrain, Kuwait, the UAE, Cyprus, and specific areas in Lebanon.
Check Point says the targeting intensified on Feb. 28, aligns with missile activity, and is consistent with Iran using camera compromise for operational support and battle-damage assessment — potentially even before missile launches. The infrastructure they tracked used commercial VPN exit nodes like Mullvad, ProtonVPN, Surfshark, and NordVPN, plus VPS infrastructure. That’s exactly the kind of thing we’ve talked about conceptually for years: cyber reconnaissance directly supporting kinetic warfare.
So now put those two stories next to each other.
On one side, you have Iranian-linked actors scanning exposed digital infrastructure to support missile operations. On the other, you have a destructive wipe against a major U.S. med-tech company being claimed as retaliation tied to the war. In this conflict, cyber and physical operations are one and same.
Then layer in the infrastructure threat picture:
The Register reported that Iranian state-affiliated channels on Telegram circulated slides titled “Iran’s New Targets,” listing facilities tied to Amazon, Microsoft, IBM, Palantir, Google, Nvidia, and Oracle. The posts described these as the “enemy’s technology infrastructure,” gave locations and facility descriptions, and framed the war as expanding into infrastructure warfare. The same report said Iran had already conducted aerial attacks against three AWS datacenters in the Middle East, one in Bahrain and two in the UAE, disrupting regional cloud providers and forcing customers to shift disaster-recovery plans.
That’s wild, because now the targeting list is not just military sites or government systems. It’s cloud, AI, research, regional support infrastructure, and the private-sector companies that keep all of that running.
Rapid7’s threat analysis fits that picture too. They’re explicitly warning that Iranian activity is likely to intensify through phishing, social engineering, credential misuse, and scanning of internet-facing infrastructure.
They call out APT35 — Charming Kitten — as a long-running spear-phishing and credential-harvesting actor, APT42 as closely associated with surveillance and social engineering, and MuddyWater and OilRig as important MOIS-linked espionage groups in the current crisis environment. They also stress that sudden spikes in probing of remote access portals, VPN gateways, cloud services, and public web infrastructure should be treated as possible precursors to intrusion.
Broader Escalation Pattern
That’s why Stryker matters: not just because a huge healthcare-adjacent company got hammered, but because it may be part of a broader escalation pattern.
If you’re a defender, the lesson here is not just “patch faster” or “watch your MDM settings,” though both matter. It’s that geopolitical conflicts are now spilling into ordinary enterprise environments much faster and in more destructive ways than a lot of companies are prepared for.
If this attack really did move through admin accounts into Intune and then into a mass wipe of corporate and personal devices, it’s a brutal reminder that the blast radius of enterprise trust is bigger than most people think.