- Vulnerable U
- Posts
- Mythos and Glasswing: Did Anthropic Break the Internet?
Mythos and Glasswing: Did Anthropic Break the Internet?

Mythos is here! The internet is doomed! That’s been the early reaction, anyway.
Here is what we actually know - it's been so successful at finding security vulnerabilities that if they released it, they're worried about national security, and the sanctity of the internet in general. They've given the tool to 40 companies they consider critical infrastructure and they're allowing these people to use Mythos to try to find and then subsequently fix all of the vulnerabilities that it would be good at finding before this fallout could possibly happen.
I’ve gotten more hate about this story than anything in a long time on social media. People are absolutely revolting, saying it must just be marketing hype. But let me give you some inside baseball: I've gotten to talk to people who run security for some of the people on this list that are telling me that the claims are real, that they are surprised at the amount and quality of the security vulnerabilities that this thing has been able to find.
Of course, Anthropic is incentivized to overhype this. I've been super critical of all of the frontier model companies coming out and being like this thing that we just built is so dangerous. That being said, when we're talking about the ability to find security vulnerabilities, Opus was already getting crazy good at this.
If you want to hear me talk about this for literal hours, check my live stream archive from this week - (specifically here and here) I pull up and react to TONs of hype and criticism of Mythos and talk about where I think this is all going.
I also wrote this tweet while live, responding to all the hype (click the image to go to the full write-up):
Some additional thoughts on all of this:
Finding Bugs vs Exploiting Them
I've been using Opus 4.6 for vulnerability research. I will say in the last week I've been able to find vulnerabilities in browsers using Opus. What I've not been able to do is write exploits. There's a big difference between finding a vulnerability and actually developing a proof of concept and exploiting it.
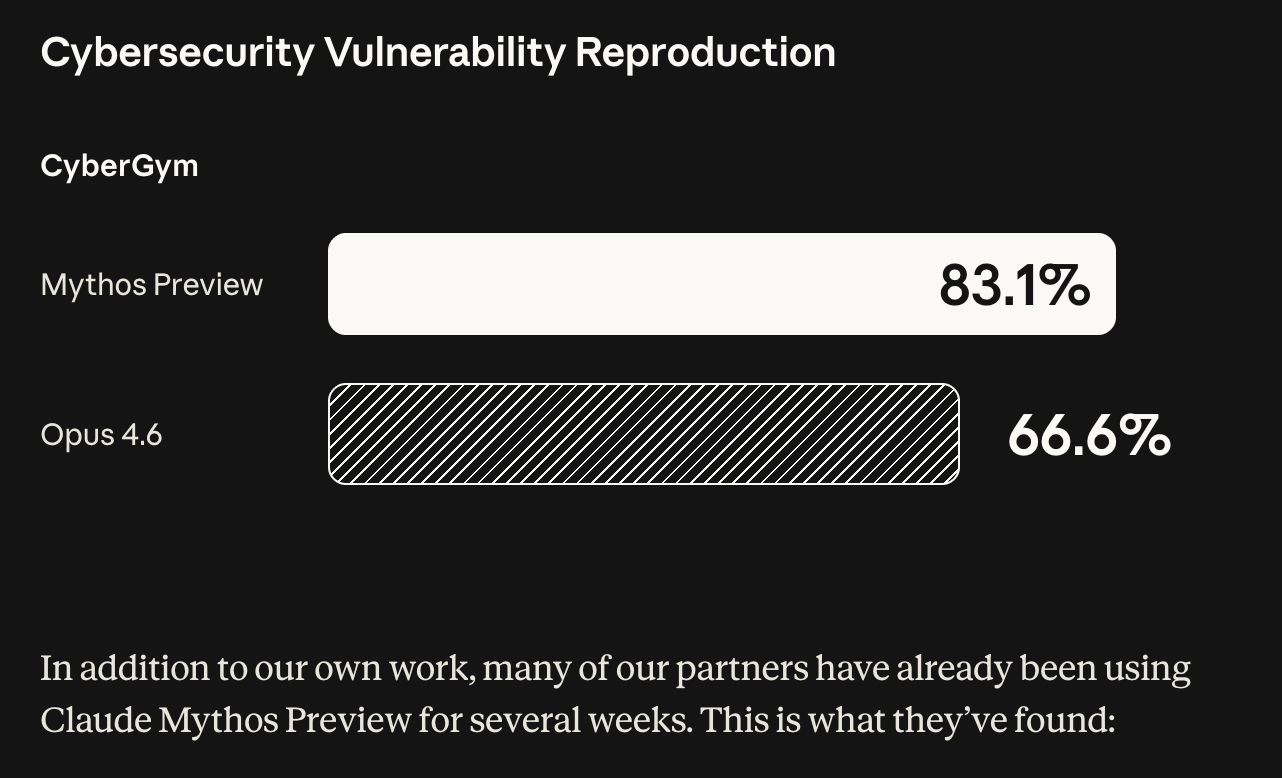
I've done enough validation to believe that I have found bugs of some severity with Opus 4.6. What they're saying they have access to right now is the percentage of trial models that actually generated a successful exploit. That is where things get scary.
This Feels Different
It takes a lot of time and tokens and direction to even find bugs. And then there's a small sliver that could actually exploit. What they're saying now is that sliver jumps dramatically. This is one of the charts that has scared me.

We have found Mythos is capable of identifying and exploiting zero day vulnerabilities in every major operating system and every web browser.
Engineers with no formal security training have asked Mythos to find remote code execution vulnerabilities overnight and woken up the following morning to a complete working exploit validated by experts.
That is a different world.
The Real Problem Isn’t Anthropic
One of the issues here is not whether Anthropic can contain this. The point is that we now know that this is possible. So that means it is coming. Irregardless of Anthropic, it's coming. Even if it doesn't leak, there's distillation. We know that models are being distilled. The capability exists now.
The Dangerous Gap
If the latest AI makes it cheaper than ever to find vulnerabilities and exploit them, it also makes it cheaper to find and fix them. The problem is when this new tool is only available to a privileged few. How fast do you think critical infrastructure can use the latest AI agent and recode itself? Do you think the water plant in the middle of Ohio is going to be able to use the latest AI agents to make sure that they are vulnerability free?
There is going to be a huge lag time.
There is no world where this instantly gets democratized and all critical code is suddenly secure. When's the last time you updated your firmware on your router.
What Happens Next
Software security was originally limited to the number of people that could execute it. What happens now if a single person can act like that or act like 100 with the right model and a couple of bucks?
What happens when every single piece of software we rely on can be exploited in a loop with a few hundred dollars of compute? In the long run, software gets more secure out of necessity.
But the in between is a scary time period where everyone is just constantly getting hacked.
We're just trying to buy some time.