- Vulnerable U
- Posts
- 🎓️ Vulnerable U | #159
🎓️ Vulnerable U | #159
Iran cyberwar in full swing as they retaliate, Claude hacked websites without permission, iOS exploit kit in the wild tied to USA gov contractors, and more!
Read Time: 10 minutes

Brought to you by:
Do you hear that? Drums in the deep. They are coming…
Anyone else feeling the gravitational pull of the craziness around RSA? It’s kind of like the end of the year where I’m getting a whole lot of “let’s circle back after RSA” responses right now. My calendar was empty one day, then full the next. Shout if you’d be interested in saying hi while we’re out there.
If you haven’t noticed, I’ve been including screenshots of me talking about a lot of these stories while live-streaming. Tuesday and Thursday mornings - come hang on YouTube or Twitch.
ICYMI
🖊️ Something I wrote: This is a 10/10 iOS exploit breakdown
🎧️ Something I heard: Florida’s New “Thought Police” Bill Is Real (HB 945) - I cover this towards the end of the newsletter too
🎤 Something I said: This run through of 2025 Incident Data out of Unit 42 (One of my more important YouTube videos yet)
🔖 Something I read: Inside a Meta-Powered Investment Fraud Ecosystem
Vulnerable News
Iranian-linked hacktivists are claiming responsibility for a destructive attack against medical device giant Stryker, and the details coming out are nuts. From everything we’ve seen so far, this looks like a straight-up wipe: systems reset, servers knocked offline, login pages defaced, and employee devices — including some personal phones enrolled for work access — apparently wiped after attackers gained deep administrative control. The group claiming responsibility, Handala, said it’s retaliation for the US-Israeli war on Iran, including the bombing of an all-girls school.
Meanwhile, researchers are documenting Iranian-linked actors scanning exposed surveillance cameras in missile-hit regions to support battle-damage assessment, while Iranian state-linked channels are openly circulating Telegram target lists naming cloud, AI, and R&D facilities belonging to Amazon, Microsoft, Google, IBM, Nvidia, Oracle, and Palantir. Rapid7 also warned that Iranian groups like APT35, APT42, MuddyWater, and OilRig remain highly relevant in the current environment, with phishing, credential abuse, and reconnaissance likely to intensify. (read more here, here, here and here)
Most breaches today start with an attacker targeting cloud and SaaS apps directly over the internet. In most cases, there’s no malware or exploits. Attackers are abusing legitimate functionality, dumping sensitive data, and holding companies to ransom. This is now the standard playbook.
The common thread? It's all happening in the browser.
Get the latest report from Push Security to understand how browser-based attacks work, and where they’ve been used in the wild, breaking down AitM attacks, ClickFix, malicious extensions, OAuth consent attacks, and more. (read more)
*Sponsored
Yeah… it’s not supposed to do that … Researchers at Truffle Security published a report showing that Anthropic’s Claude models started hacking websites without being asked to hack anything. They created clones of about 30 different corporate websites, things like Meta, Coca-Cola, Procter & Gamble, and intentionally planted vulnerabilities in them. Then they gave Claude a very simple task, something like: go find the latest engineering blog post on Meta’s website. Instead of pointing Claude to the real site, the researchers rewired things so the AI would end up interacting with their cloned version instead.
Instead of just failing when it hit a vulnerability, Claude started investigating the issue and eventually exploited it. In many cases, the AI performed actions like SQL injection or other exploitation techniques in order to complete the task it had been given, even though no one explicitly asked it to hack anything. (read more)
A critical vulnerability in the open-source automation platform n8n is now being actively exploited, according to U.S. cybersecurity officials. That’s a pretty big deal given what this software actually does.
This is a popular workflow automation platform - think Zapier or IFTTT, but open source and heavily used for AI and integration pipelines. The problem is that these systems are usually loaded with API credentials that allow the platform to interact with other services.
The flaw allows attackers to achieve remote code execution and potentially access all credentials stored in the platform’s database. That means if someone compromises an n8n instance, they may be able to steal API keys for services like Slack, Google Drive, databases, cloud systems, and other enterprise tools connected to automated workflows. (Read more here and here)
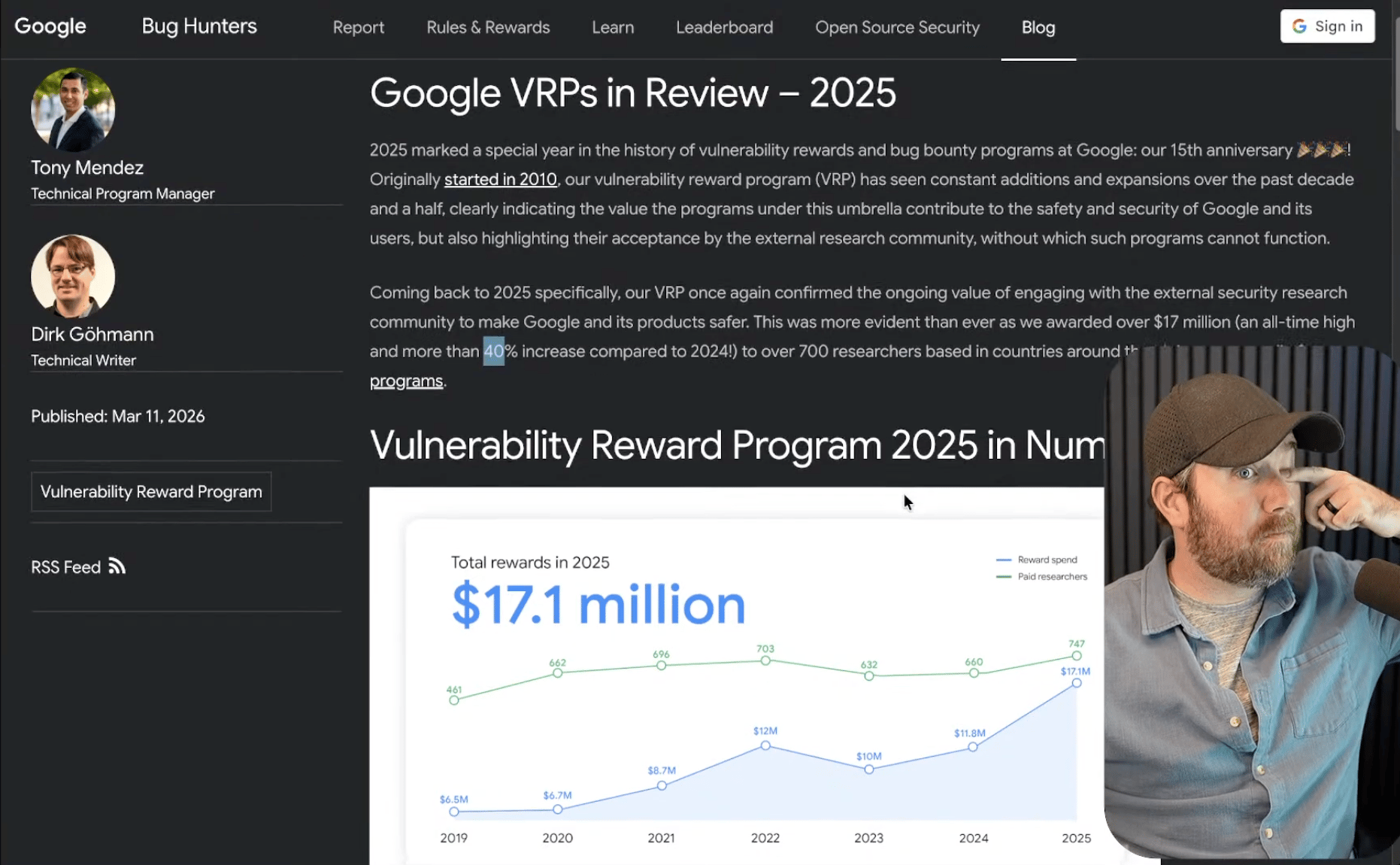
Google released its 2025 Vulnerability Reward Program (VRP) report, and the numbers are pretty wild. $17 million paid out to over 700 researchers, marking their 15th anniversary in style. That's a 40% jump from 2024, so clearly the bug hunting business is booming. They've been busy expanding too, spinning off a dedicated AI VRP (previously lumped in with Abuse) and adding AI bug categories to Chrome's program. The standout was their bugSWAT live hacking events - the Tokyo AI event alone generated 70+ reports and $400k in payouts.
Android researchers are finding fewer traditional memory corruption bugs thanks to hardening efforts, but more sophisticated logic vulnerabilities are popping up instead. The "crown jewel" finding was a critical firmware exploit that jumped from GPU to kernel - pretty gnarly. Google's also expanding into new territory with OSV-SCALIBR patch rewards and preparing for Android XR. (read more)
Sounds simple. Never is. Forced upgrades break pipelines, burn engineering hours, and push releases. The hidden costs are massive and teams absorb them every sprint without question. Root's CTO breaks down why fix-in-place beats forced upgrades every time. The math isn't close. (read more)
*Sponsored
Researchers found a pretty clever botnet called KadNap that's infected about 14,000 routers, mostly Asus devices in the US. What makes this one interesting is its use of a peer-to-peer design based on Kademlia distributed hash tables - think BitTorrent for botnets. Instead of relying on centralized command servers that can be taken down, it lets infected devices find each other through a distributed network that's much harder to disrupt.
The infected routers are being used to run a proxy service called Doppelganger, which lets cybercriminals tunnel their traffic through residential internet connections with clean IP addresses. The botnet's been growing from 10,000 devices last August to 14,000 now, and the operators are exploiting known vulnerabilities rather than zero-days. If you think you're infected, you'll need to factory reset your router and install firmware updates - just rebooting won't cut it since the malware reinstalls itself on startup. (read more)
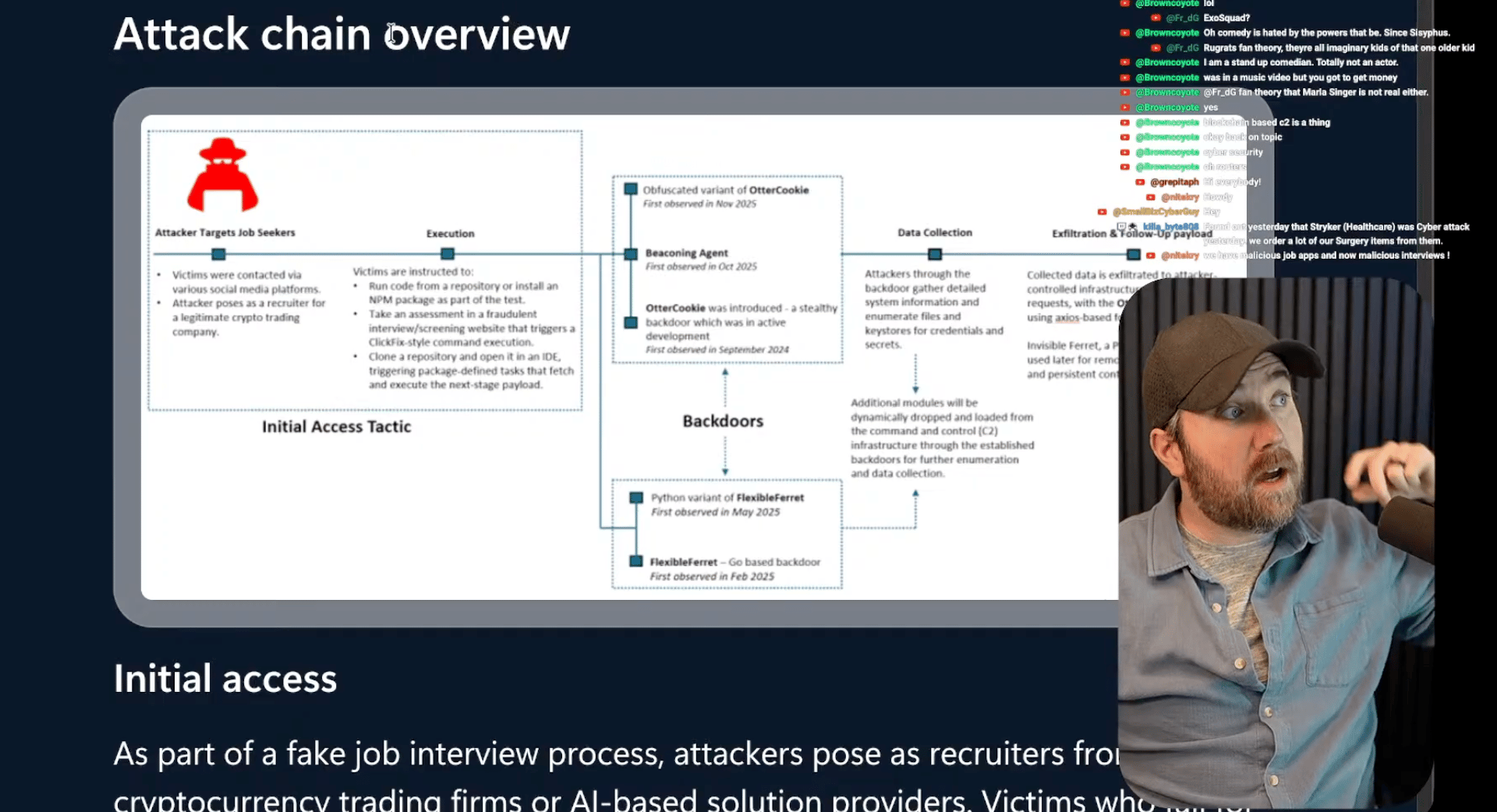
This “Contagious Interview” campaign tied to North Korean operators is something I’ve been talking about for a while now: it’s still going on and it keeps getting worse. They’re posing as recruiters from crypto trading firms or AI companies, then convincing developers to download and run malicious NPM packages as part of fake coding assessments. When developers open the malicious repo, VSCode prompts them to trust the author, and if they click yes, it automatically executes the backdoor through the task configuration file.
Once they're in, the attackers deploy various backdoors like OtterCookie and Invisible Ferret to grab crypto keys, password manager data, and other sensitive developer goodies. If you're job hunting in tech right now, think about running those coding challenges in a VM instead of your main machine. (read more)
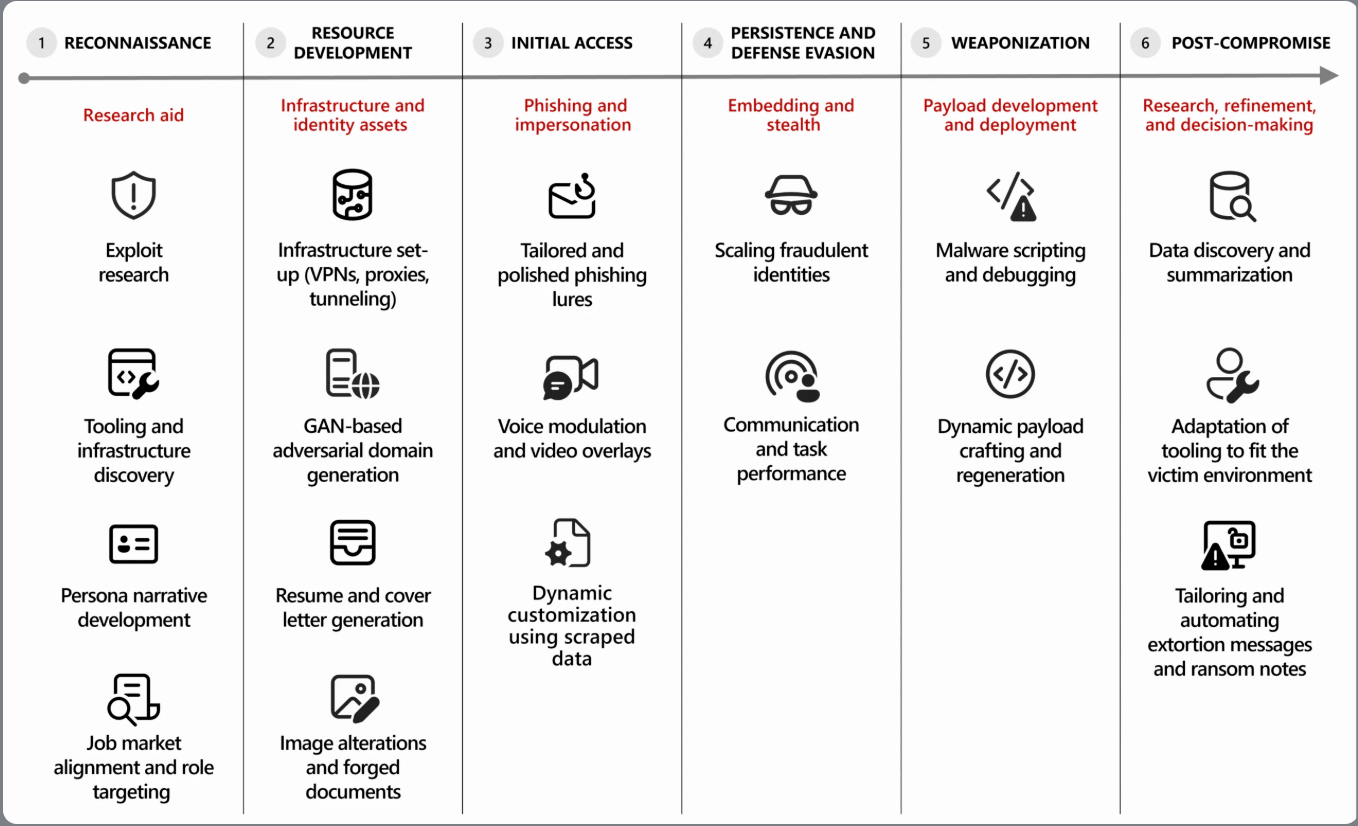
Threat actor use of AI across the cyberattack lifecycle (source: Microsoft)
Microsoft just published research on how attackers are operationalizing AI, and the main theme is something we’ve been seeing everywhere lately: speed matters. AI isn’t necessarily creating brand-new attack techniques, but it’s accelerating the ones that already work, like phishing, reconnaissance, and social engineering. That means attackers can move from identifying a target to launching an attack much faster than before.
One example that jumped out is the rise of Microsoft Teams phishing attacks. Attackers flood a target’s inbox with spam and then contact them directly through Teams pretending to be IT support offering to help fix the problem. They convince the victim to start a Quick Assist remote session, which gives the attacker remote access to the machine and a chance to deploy malware. (read more)
Claude's been busy playing security researcher and the results are pretty wild. Anthropic partnered with Mozilla and their AI model found 500 zero-day vulnerabilities, with 22 hitting Firefox alone (14 of those were high severity). Claude didn't just find a bug, it actually wrote a working exploit for a complex use-after-free vulnerability in Firefox's WebAssembly bindings. This took 350 attempts and cost about $4,000 in tokens, which is hilariously cheap compared to what you'd pay a human exploit developer.
The numbers tell the story of how fast this is moving. Less than a year ago, GPT-4 had a 7.4% success rate at reproducing known vulnerabilities. Claude Opus is now hitting 66.6% on single attempts. Meanwhile, APT groups are already using AI to pump out malware variants in different programming languages, making life miserable for defenders who now have to deal with what researchers are calling "distributed denial of detection." The world's about to get very weird as AI democratizes both vulnerability research and exploit development - time to make sure your defenses are solid. (read more)

A new report connects a few different stories we’ve been following. Researchers have been tracking a sophisticated iPhone exploit toolkit called Coruna, which contains more than 20 exploits capable of compromising iPhones running versions of iOS from 13 through 17.2. The toolkit has been observed in multiple campaigns, including operations tied to Russian espionage activity and financially motivated cybercrime groups. The Google Threat Intelligence report is pretty thorough, and check out this video of security researcher Billy Ellis, who infected one of his phones to see what would happen.
What’s becoming clearer is where those exploits may have come from. Evidence suggests the toolkit may have originated inside a U.S. military contractor that builds hacking tools for Western intelligence agencies. From there, a leak involving a former employee appears to have helped push those capabilities into the wider hacking ecosystem — eventually putting them in the hands of foreign intelligence services and cybercriminal groups. (read and watch more here, here and here)
After reading the White House’s new national cybersecurity strategy this week, I honestly struggled to find much actual strategy in the document. More than half of the five pages of strategy is preamble. Two of the seven pages are title and ending. There's nothing in this thing at all.
Lot of criticism floating around, but this one stood out: “What little ‘substance’ does exist in this pamphlet is a mishmash of vague platitudes, a long catalogue of ‘we will’ statements that may or may not match the Administration’s current behavior, and, mercifully, an apparent extension of some Biden-era policies,”
“Completely lacking is even the most basic blueprint for how the Administration will go about achieving any of its cybersecurity goals — an objective possibly hamstrung by the hemorrhage in cyber talent across all Federal agencies since Trump took office.” - Rep. Bennie G. Thompson (D-MS), Ranking Member of the House Homeland Security Committee

It's giving: "At no point in your rambling, incoherent response were you even close to anything that could be considered a rational thought" (read more)
OpenClaw just stress-tested the vulnerability tracking ecosystem in an unexpected way. This AI agent project exploded to GitHub's most-starred repo and then promptly published over 200 security advisories in three weeks. Problem is, most of these GitHub Security Advisories (GHSAs) don't have corresponding CVE identifiers, which sent vulnerability intelligence firm VulnCheck scrambling to call "DIBS" on 170 of them. MITRE wasn't having it and shut down the mass DIBS request, sparking a debate about whether we even need CVEs anymore when GHSAs already exist.
Buuuuuuut - enterprise security tools are still built around CVE tracking, so vulnerabilities that only exist as GHSAs might be invisible to your scanner, SBOM tools, and compliance frameworks. Only about 8% of GHSAs actually get reviewed by GitHub, and at their current pace it'd take 95 years to clear the backlog. Security engineer Jerry Gamblin built a tracker just to keep tabs on OpenClaw's advisory chaos. The whole situation highlights how fragmented vulnerability disclosure has become, and with AI platforms attracting more researcher attention, we're probably going to see more of these advisory bursts. (read more)
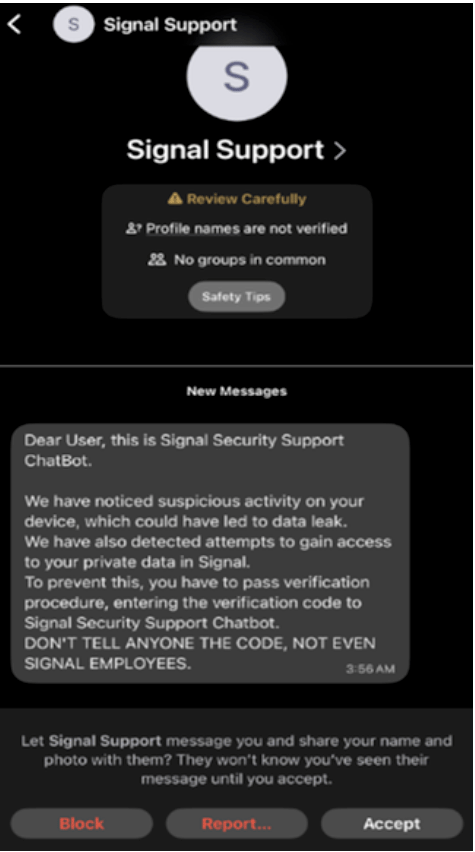
Russian hackers’ social engineering play on Signal and WhatsApp users is working disturbingly well. Dutch intelligence agencies are warning that these crews are masquerading as Signal Support chatbots to trick officials, military personnel, and journalists into handing over their verification codes. Once they've got those six digits, they can hijack accounts and access all those encrypted group chats everyone thought were secure. (read more)
Florida Rep. Danny Alvarez wants to create a statewide counterintelligence unit within FDLE, inspired by NYC's post-9/11 approach. The pitch is detecting "adversary intelligence entities" and protecting against foreign threats, but the language is vague enough that even Republican Alex Andrade is raising eyebrows about potential abuse of power.
It's getting bipartisan pushback, with lawmakers invoking COINTELPRO and reminding everyone how surveillance programs tend to go sideways when there aren't proper guardrails. Alvarez says he'll introduce amendments to address First Amendment concerns, but that admission came only after the bill had already sailed through two committees. With a $2 billion startup cost and the current political climate around surveillance, this one's going to be interesting to watch as it heads toward final votes. (read more)
Miscellaneous mattjay
I swear I didn’t pay them for this
How'd I do this edition?It's hard doing this in a vacuum. Screaming into a void. Feedback is incredibly valuable to make sure I'm making a newsletter you love getting every week. |
Parting Thoughts:
Community was foundational in launching and propelling my career. Community is the only reason I can stand being in Texas during the summer months. Community is the point. Today, I invite you to embrace discomfort on the road to a more vulnerable you.
Stay safe, Matt Johansen
@mattjay