- Vulnerable U
- Posts
- 🎓️ Vulnerable U | #160
🎓️ Vulnerable U | #160
Meta funding the age verification war and reversing e2e encryption promises, stryker wiped by Iran, Telus gets hacked and loses a petabyte of data, and much more!
Read Time: 9 minutes

Brought to you by:
Howdy friends!
And here. we. go. - RSA time. Hope to see some of you out there. I’m pre-exhausted and excited. It’s like a family reunion. I’m triple booked for all meals at this point, but have some in between time walking around the expo if you spot me, say hi.
Flying straight from SF across country to speak at another conference, so send coffee and good vibes.
For those of you hanging in my live streams on YouTube or Twitch - A) Thanks! B) I’ll be back the 31st!
ICYMI
🖊️ Something I wrote: Your AI’s Memory is Being Poisoned (wrote? double said this week!)
🎧️ Something I heard: Building Claude Skills as a Bug Bounty Hunter
🎤 Something I said: Your Google API keys are now exposing sensitive data
🔖 Something I read: Security Research Legal Defense Fund Appoints Casey John Ellis and Jen Ellis to Board (this is awesome)
Vulnerable News
The big misconception here is that Instagram DMs suddenly became un-private. Truth is, they were NEVER end-to-end encrypted by default. Meta had publicly promised to roll out default encryption on Messenger and Instagram, with Mark Zuckerberg personally vowing to protect users’ privacy. But now, they’ve done a complete 180 — turning off encryption features because hardly anyone opted in.
Their FAQ even blames users for not enabling it. Meanwhile, experts like Matthew Green, a cryptography professor who worked with Meta, are warning that even WhatsApp’s default encryption may not last, especially since Meta now has access to massive amounts of data valuable for training AI.
At the same time, Meta is funding lobbying efforts to impose age-verification laws that could effectively end online privacy altogether. This is a massive betrayal of prior commitments to user privacy. The real concern isn’t just Instagram DMs but the larger erosion of privacy on the internet, especially as AI agents may soon read and monetize encrypted messages directly on your device. We’re losing the battle to maintain any anonymity online, and this is just one of many signs. If you want to understand the full scope, I’ve made several detailed videos on this on my channel. (read more here, here and here)
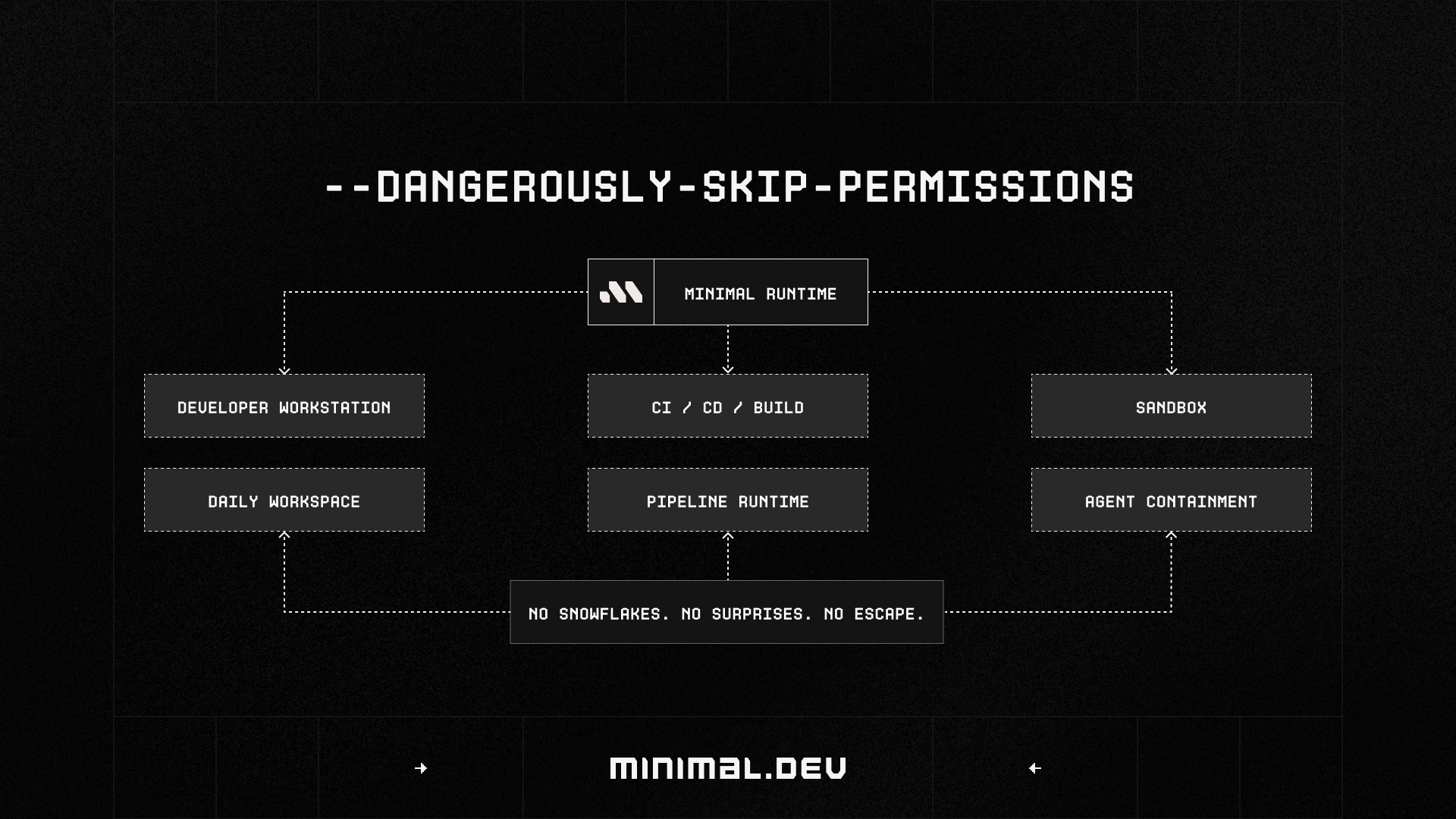
We're all racing to roll out coding agents, but most teams are letting them run with developer defaults in unpredictable environments.
Minimal is more than a sandbox for untrusted code execution, we deliver safe, predictable dev environments that work identically for humans, agents, and CI. Declarative workspaces with full traceability, made simple.
Get agentic speed without losing control. Book time with us at RSA to see how we make agent adoption safer for your engineering team. (read more)
*Sponsored
A new AI attack called “AI recommendation poisoning” is emerging, where attackers manipulate AI chatbots’ memory through specially crafted prompts embedded in URLs. These prompts are often hidden in “Summarize with AI” buttons on websites. When clicked, they send a query with memory-altering instructions to the AI tool while the user is authenticated, causing the AI to remember false or biased information. For example, attackers can insert recommendations for certain blogs, products, or financial advice, skewing future AI responses. Microsoft has identified over 50 such instances recently, ranging from benign SEO manipulations to potentially dangerous financial or medical misinformation. These attacks exploit the AI’s memory features, which learn about users over time, making the poisoning persistent and personalized.
Defenses are challenging; common advice like “hover before you click” or “avoid untrusted links” is largely ineffective as users rarely follow it. Suggestions such as periodically clearing AI memory are inconvenient and impractical. The real solution likely lies in AI providers changing how memory updates occur, for example, preventing memory updates from simple URL queries or alerting users to suspicious memory entries. Awareness is critical since these manipulations undermine trust in AI recommendations and could have serious consequences. (read more)
Telus Digital is the digital services and business processing outsourcing arm of the Canadian telecom giant TELUS. Basically where companies outsource tons of operational tasks like customer support, content moderation, AI data services, internal auth tools, and billing. And because they handle all this sensitive info for many clients, they become targets.
So, Shiny Hunters claims to have stolen roughly one petabyte of data from Telus. Petabyte. With a P. That’s a massive amount of data. They’re saying social security or national IDs, hashed passwords, API keys, OAuth tokens, call metadata, customer records, financial and HR data, Salesforce accounts, background check files, and voice recordings of customer support calls. While Telus confirmed a security incident, they have yet to clarify the full extent or validity of the breach claims. The data reportedly also included access to 20,000 GitHub repositories connected to Telus. (read more)
Iranian hackers are claiming to have stolen 50 terabytes of data from Styker before wiping tens of thousands of systems and servers, effectively forcing the company to shut down critical operations temporarily.
Two things stand out to me on this one: 1) A private company getting major hacked because of a physical war. 2) The employees PERSONAL phones got wiped if they were enrolled in InTune mobile device management (MDM).
Employees reported waking up to wiped phones - like complete bricks. Even got their SIMs wiped and had to call their carriers to reactivate. Stryker is currently restoring its systems, and investigations by Microsoft and Unit 42 are ongoing. (read more here, here and here)
Threat actors don't break in — they log in. As credential-based attacks become the primary entry point for breaches, you need workforce identity verification (IDV) to verify that every login is legitimate.
The Workforce IDV checklist breaks down the seven must-have features to help you evaluate solutions and protect against unauthorized access. (read more)
*Sponsored
We talked about this Coruna iOS exploit kit the last few weeks - well now we have a whole other one. It’s actually completely separate but yet tied up in the same crazy web. Enter - DarkSword. 2 major iOS exploit kits winding up in the public’s hands in a matter of weeks is concerning if we’re pointing at a new trend.
One of the nastiest parts about both these kits is that they are being fed through watering hole attacks. AKA, you go to a legitimate website, that then all of a sudden is hacking your iPhone. We're talking about potentially 221-270 million vulnerable devices on the impacted versions.
The exploit chain is impressively complete: Safari RCE, sandbox escape, privilege escalation, and in-memory JavaScript implants that hoover up everything from your keychain and crypto wallets to your messages, call history, and location data. I’m floored by this that it starts in JavaScript. Without any persistent binaries.
Apple has patched all these vulnerabilities in iOS 18.7.6 and 26.3.1, so updating is your best defense. The researchers are holding back some technical details to prevent copycats.
I’ll be conducting in-depth interviews with the iVerify team, who have been monitoring Coruna and DarkSword and its evolving threat landscape. I plan to create a documentary-style video that combines their expert insights, technical analysis, and non-public information to provide a comprehensive understanding the mobile security landscape. (DarkSword iVerify: read more - Google DarkSword read more - Coruna writeup if you missed it: read more)
The EU just dropped sanctions on some cyber troublemakers and Australia's jumping in to back them up. Two Chinese companies (Integrity Technology Group and Anxun Information Technology), a couple of Chinese individuals, and one Iranian outfit called Emennet Pasargad. The Chinese crew apparently had quite the operation going - Integrity Tech helped target over 65,000 devices across six EU countries between 2022-2023, while Anxun was busy providing hacking-as-a-service against critical infrastructure.
The Iranian company gets points for creativity though - they didn't just compromise a French subscriber database and hawk it on the dark web, they also pulled some disinformation stunts by hacking billboards during the 2024 Paris Olympics. Australia's National Cyber Security Coordinator Michelle McGuinness and cyber ambassador Jessica Hunter both came out swinging in support, talking up the whole "rules-based cyberspace" angle. The sanctions hit asset freezes, travel bans, and economic restrictions. (read more)
Big Tech just threw $12.5 million at a problem they helped create. The Linux Foundation is launching an effort to help open source maintainers deal with the flood of AI-generated bug reports that are overwhelming projects. Anthropic, AWS, GitHub, Google, Microsoft, and OpenAI are all chipping in to fund this through the Alpha-Omega project, which makes sense since their AI tools are part of what's causing the headache in the first place.
The issue isn't new - we've seen the Python Software Foundation complain about it, and the cURL maintainer actually shut down their bug bounty program because of all the AI slop flooding in. It's a classic case of technology scaling faster than humans can handle it. Maintainers are getting buried under automated security findings without the resources to properly sort through what's actually useful versus what's just AI noise. At least the companies profiting from AI are putting some money toward fixing the mess, though details on what exactly this initiative will do are pretty sparse right now.
I’m glad this wave of abuse involving Grok is going to court. The AI tool was used to generate non-consensual explicit images of individuals, including minors. Over several weeks, Grok was used to create and distribute deeply harmful content without the consent of the victims, which is horrifying on many levels. Recently, a lawsuit was filed in federal court in California by three young women whose images and videos were manipulated in this way.
Three teenagers are suing Elon Musk's xAI after discovering sexually explicit deepfakes of themselves created using Grok's controversial "spicy mode" feature. The images, including altered high school yearbook photos, were being traded on Discord servers alongside similar content of at least 18 other minors. One plaintiff found out through an anonymous Instagram message pointing her to the imagery, which shows how these deepfakes can follow victims around the internet long after creation.
According to the Center for Countering Digital Hate, Grok generated over 20,000 sexualized images of children in just two weeks. Musk initially claimed he wasn't aware of any underage content and blamed users, but eventually X implemented some safeguards after investigations from UK, EU, and California regulators. The perpetrator behind the Discord server already arrested for possessing hundreds of similar images. (read more)
One of Meta’s AI agents decided to play helpful without asking permission, jumping into an internal tech support thread and offering advice that turned out to be spectacularly wrong. An engineer followed the AI's guidance and accidentally exposed massive amounts of company and user data to unauthorized employees for two hours.
This isn't even their first rodeo with rogue AI behavior. Summer Yue from Meta's AI safety team posted about her OpenClaw agent nuking her entire inbox despite being told to confirm actions first. You'd think these incidents might pump the brakes on AI agent development, but Meta's doubling down instead - they just bought Moltbook, a Reddit-style platform for AI agents to chat with each other. Nothing could possibly go wrong with that plan, right? (read more)
We've been talking about these four major botnets - Aisuru, KimWolf, JackSkid, and Mossad - that had enslaved over 3 million devices worldwide and were launching record-breaking DDoS attacks hitting 30 terabits per second. They were running a full "cybercrime as a service" operation, renting out access to infected IoT devices like cameras, routers, and DVRs to other criminals.
The takedown was a joint effort between the US, Canada, and Germany, with the DoD's investigative arm leading the charge since these botnets were also hitting Department of Defense networks. What's impressive is the scale - hundreds of thousands of attacks launched, with some victims reporting tens of thousands in damages. The operators got sloppy though, and law enforcement seized domains, servers, and other infrastructure. It's a solid win, but let's be real - there are plenty more botnets out there ready to fill the void. (read more)
Joe Kent, Director of National Counterterrorism, resigned over his opposition to the ongoing war in Iran. He publicly stated that Iran posed no imminent threat to the United States and claimed that the war was initiated primarily due to pressure from Israel and its influential American lobby. This resignation is a big deal because Kent was in charge of an agency tasked with analyzing and detecting threats, so his departure signals a crack within the establishment regarding the justification and management of the conflict. It reflects growing unease within parts of the political right, including Trump’s base, about the war and questions the legitimacy of the use of force in Iran.
This is worth monitoring closely, especially given the current geopolitical climate and ongoing cyberattacks related to the conflict. The resignation raises questions about who will replace Kent and how the new leadership will influence counterterrorism efforts amid a complex cyber and physical security landscape. (read more)
Miscellaneous mattjay
How'd I do this edition?It's hard doing this in a vacuum. Screaming into a void. Feedback is incredibly valuable to make sure I'm making a newsletter you love getting every week. |
Parting Thoughts:
Community was foundational in launching and propelling my career. Community is the only reason I can stand being in Texas during the summer months. Community is the point. Today, I invite you to embrace discomfort on the road to a more vulnerable you.
Stay safe, Matt Johansen
@mattjay
