- Vulnerable U
- Posts
- 🎓️ Vulnerable U | #161
🎓️ Vulnerable U | #161
Trivy and LiteLLM nightmare from TeamPCP hacking GitHub workflows, Hong Kong privacy issues, FCC bans foreign routers, and much more!
Read Time: 9 minutes

Brought to you by:
Howdy friends!
Writing you from Boston where I’m out here to speak at PAX East. Gave a talk about security in the gaming industry back in the fall at PAX West and it was a packed house so the organizers had us come do the repeat on the other coast. The only bummer here is that it was back to back with RSA so I’ve been on the road already since last Saturday for BSidesSF.
Had a great week out there. Brought some of the VulnU team with me and for one of them it was their first security con. He said he’d never seen a con where the attendees so gladly talked to everyone at the booths and that the booths didn’t need to resort to tricks to get people to come in. (BSidesSF. Not RSA, RSA was a full circus) - And I agree, most BSidesSF booths were staffed by the founders and lots of them were founders who were recently practitioners.
Of course, the best parts of the week were all the side events. Decibel Oasis was STACKED with some really fantastic people and content. Eric, the CISO of Writer held a small AI meetup where Jason Haddix and Daniel Miessler talked the future of AI in Offensive security. Axios and Varonis (coincidentally the sponsor of today’s newsletter) had an awesome event where they interviewed an FBI agent on Iran.
Thanks to all of you who took the time to pull me aside and tell me how much my content means to you. It really keeps me going. I heard from CISOs to SOC engineers to sales folks that watched/read what I do every week. Means the world, thank you.
And of course just the absolute family reunion it is all week of people I’ve been seeing out there since ~2009. Cheers to friends/family new and old. You make this industry worth being in.
 |  |
 |  |
ICYMI
🖊️ Something I wrote: The war on privacy continues. And a double header.
🎤 Something I said: AI is infesting our browsers (not just the AI ones like Comet)
🔖 Something I read: This paper on Claude Code deployed in an autoresearch loop to discover novel jailbreaking algorithms
Vulnerable News
If you use LiteLLM, check your version right now. Run pip show litellm - if you're on 1.82.7 or 1.82.8, assume everything on that machine is compromised and rotate every credential that environment could touch. On March 24th, two malicious versions were published to PyPI containing a multi-stage credential stealer that harvested SSH keys, cloud provider creds, Kubernetes configs, API keys, and shell history.
The packages were up for about three hours, but with 3.4 million daily downloads, that's a lot of exposure. LiteLLM has engaged Mandiant for forensics and paused all new releases. (LiteLLM's security advisory)
LiteLLM got popped because their CI/CD pipeline was doing the right thing - running Trivy, Aqua Security's vulnerability scanner, as a security gate. But Trivy itself had already been compromised. A threat group called TeamPCP used credentials from a prior Aqua Security breach to force-push malicious code to 76 of 77 release tags in trivy-action on GitHub.
When LiteLLM's pipeline ran Trivy, the compromised action stole the maintainer's PyPI token right out of the GitHub Actions runner. From there, the attackers published the backdoored packages using legitimate credentials, passing all integrity checks. The GitHub issue reporting the compromise was closed as "not planned" and flooded with bot comments, suggesting the maintainer's account may have still been under attacker control.
Beyond the Trivy to LiteLLM chain, they hit Checkmarx's KICS GitHub Action, spread to npm, Docker Hub, and VS Code extensions, defaced Aqua Security's entire internal GitHub org, deployed a wiper targeting Iranian systems, and appear to have partnered with Lapsus$ to monetize roughly 300GB of stolen credentials.
They're running their C2 on blockchain-based infrastructure that's essentially takedown-proof. This is probably the biggest supply chain incident of the year so far. (read more, Krebs here, Wiz here, Aikido here, Socket summary here, and Socket talking about how they’re teaming up with ransomware groups here, )
AI agents, copilots, and embedded LLMs are already operating across enterprise environments faster than security teams can track them. The bigger risk isn’t just bad prompts or jailbreaks. It’s that most organizations don’t know which AI systems exist, what data they can access, or how they behave in production.
This deep dive from Varonis breaks down why AI security starts with data visibility, how shadow AI emerges, and how to secure AI across its full lifecycle.
*Sponsored
Like I needed more beef with VPN providers. Apparently, they might open you up to warrantless surveillance. Tulsi Gabbard got a letter from some top intelligence officials asking the question, “Hey, you know how we do that whole warrantless government spying thing against non-US citizens? How about people using a VPN?” VPNs commingle a bunch of traffic into a single server, so maybe we can't tell the US citizens from the foreigners, which could open US citizens up to the US government's secretly compelling service providers for warrantless search and seizure of their comms.
The question comes up after some declassified intelligence community guidelines that say a person whose location is unknown is presumed to be a non-US citizen unless there's specific information to the contrary. Well, guess what VPNs are designed to do? Make your location unknown. That's by design.
We have no evidence that this is happening, but this letter is asking Gabbard to publicly clarify what impact, if any, VPNs have on Americans' privacy. People pay money to VPN providers to be more private, not less. I hate a lot of VPN providers for a myriad of reasons, including how their marketing is about protecting you from hackers, even though HTTPS exists. Don't get me started. That’s a whole other rant. (read more)
This is what's coming everywhere: Hong Kong just made it an illegal, criminal offense to not give the police your passwords or whatever decryption assistance to access all personal electronic devices, including cell phones and laptops. This legal change includes U.S. citizens in Hong Kong arriving and transiting through the airport. Hong Kong International Airport has authority to take and keep any personal devices that they claim are linked to national security defenses, which is whatever the hell they want it to be.
I'm not pointing this out to say this is a Hong Kong thing, even though it is, and you should all know about it. This is about the war on encryption and the war on privacy and the war on VPNs and the age verification trend and everything about de-anonymizing you and giving power of your information, your privacy, and your information security over to the government. (see more)
ClayRat, a Russian Android spyware operation that launched in October, has already face-planted spectacularly by December. The malware had some decent capabilities - intercepting SMS, call logs, taking photos, screen recording, the usual RAT stuff - and was pulling in subscribers at $90/week or $300/month through Telegram channels. But the developer made every rookie mistake in the book: plaintext passwords, weak obfuscation, obvious command names, and openly advertising.
The whole thing unraveled when authorities arrested the suspected developer, a student in Krasnodar, and all the C2 servers went dark. Solar (the Russian security firm that tracked this) noted that ClayRat followed the same trajectory as other amateur malware operations like the Gorilla banking trojan - brief spike in activity, then operational security failures lead to a quick collapse. It's almost impressive how quickly someone can build a 600+ sample malware operation and then torpedo it through basic security mistakes. (read more)
The FCC just banned importing new consumer routers made overseas, pointing fingers at Chinese hacking groups like Salt Typhoon and Flax Typhoon as the reason. China apparently controls about 60% of the consumer router market, so this is going to shake things up. Existing routers are fine, but new foreign-made ones need approval from DoD or DHS to get through customs.
The FCC didn't actually provide evidence that US-made routers are more secure. In fact, Salt Typhoon has been busy exploiting Cisco routers (American-made), and Flax Typhoon targeted both US and foreign devices in their massive botnet operation. The whole thing feels a bit ironic when you consider that FCC Chairman Carr, who's pushing this ban, also voted to scrap cybersecurity rules for telecom operators just a few months ago. (read more)
Remember when iPhone exploits were basically only hackable by nation-states? Those days might be over. We’ve covered DarkSword but latest update! The source code for it just leaked on GitHub, and security folks are properly freaking out about it. This thing can target hundreds of millions of iPhones, and now instead of being limited to fancy government hackers, it's potentially available to anyone who can navigate GitHub.
This comes right after researchers discovered DarkSword and another similar kit called Coruna being used in the wild. About 25% of iPhones are still running vulnerable iOS versions, partly because users are apparently not thrilled with iOS 26's AI features. Apple's pushed some patches and keeps pushing Lockdown Mode, which seems to be holding up well against these exploits. But the broader trend here is concerning - we're seeing iPhone exploit development scale up from boutique nation-state operations to something approaching mass market availability. Is this iOS’s WannaCry moment?(read more)
A months-long investigation by Rapid7 Labs found Chinese state hackers (Red Menshen) planting BPFdoor backdoors deep inside telecom networks worldwide. It operates at the Linux kernel level using Berkeley Packet Filters (BPF), so it never actually opens listening ports. Instead, it passively monitors network traffic and only activates when it receives specially crafted "magic packets."
The malware even masquerades as legitimate services like HP ProLiant server management and Docker processes to blend into telecom infrastructure. Since these networks carry government communications and can enable population-level surveillance through protocols like SCTP (used in 4G/5G signaling), we're talking about national security implications. Rapid7's released detection tools, but this represents a troubling shift toward deeper, kernel-level persistence that traditional security tools struggle to catch. a la BRICKSTORM if you’ve seen my coverage on that. (read more)
Whats a vuln without a name. "ShadowPrompt" can let any website hijack Claude's Chrome extension and send it malicious prompts. The attack chained two flaws: Claude's extension trusted any *.claude[.]ai subdomain, and there was a DOM-based XSS in an old Arkose Labs CAPTCHA component running on a-cdn[.]claude[.]ai. Put them together, and an attacker could silently inject prompts into Claude's sidebar from any website using an invisible iframe - no clicks, no permissions.
The demo shows it stealing Google account tokens, reading your Drive, exporting chat history, the works. With 3 million users, that's a lot of potential victims. The good news is both Anthropic and Arkose Labs moved fast on fixes once disclosed. Anthropic locked down the origin checking to only allow exactly https://claude[.]ai, and Arkose patched their XSS. If you're using the Claude extension, make sure you're on version 1.0.41 or higher. (read more)
Push Security spotted a fresh phishing campaign going after TikTok for Business accounts using some slick AITM (Adversary-in-the-Middle) phishing kits. The attackers registered a bunch of domains on March 24th within a 9-second window, all following the "welcome[.]careers*[.]com" naming pattern. Victims get tricked into clicking malicious links that lead to either fake TikTok Business pages or Google "Schedule a Call" clones, ultimately serving up credential-stealing login pages behind Cloudflare bot protection.
At first glance, targeting TikTok seems weird compared to the usual Google/Microsoft focus, but it actually makes sense. TikTok's become a playground for malware distribution (remember those AI-generated CapCut "activation" videos that hit 500k views?) and crypto scams. Plus, most business users log into TikTok with their Google accounts anyway, so attackers get a two-for-one deal - compromised TikTok access plus all those juicy Google Workspace goodies. It's the same playbook we've seen with Google Ad Manager takeovers. (read more)
The Intellexa spyware saga just got spicier. Tal Dilian, the founder behind the Predator spyware that's been causing headaches globally, got slapped with an 8-year sentence by a Greek court for his role in the "Greek Watergate" scandal. But instead of quietly heading to appeals court, he's dropping some not-so-subtle hints that the Greek government was pulling the strings all along. Dozens of phones belonging to government ministers, journalists, and opposition leaders got hacked using his tool, and now he's saying he won't be the "scapegoat."
Several senior Greek officials resigned when the whole mess came to light, but mysteriously none of them got convicted. Dilian's basically calling it a cover-up and says he's got evidence to share with regulators. The guy's already been sanctioned by the US after Predator was caught targeting American officials and journalists, so his credibility might be questionable. But if he's got receipts showing government authorization for these hacks, this could get real messy for the Mitsotakis administration. (read more)
Medical device giant Stryker is finally getting back on their feet after Iranian hackers absolutely demolished over 200,000 of their devices two weeks ago. The attackers weaponized Microsoft Intune's own device wipe feature - turning the company's management tools against them. The impact here was pretty insane. Hospitals in Maryland had to fall back to radios for communication, some surgeries got cancelled due to missing implants, and Stryker employees stationed at hospitals couldn't do their jobs.
Stryker initially insisted no malware was involved in the attack, but they quietly walked that back in Monday's update. Turns out the hackers did use malicious files to hide their tracks while lurking in the systems. Palo Alto's Unit 42 team has given them the all-clear that the bad guys are gone. (read more)
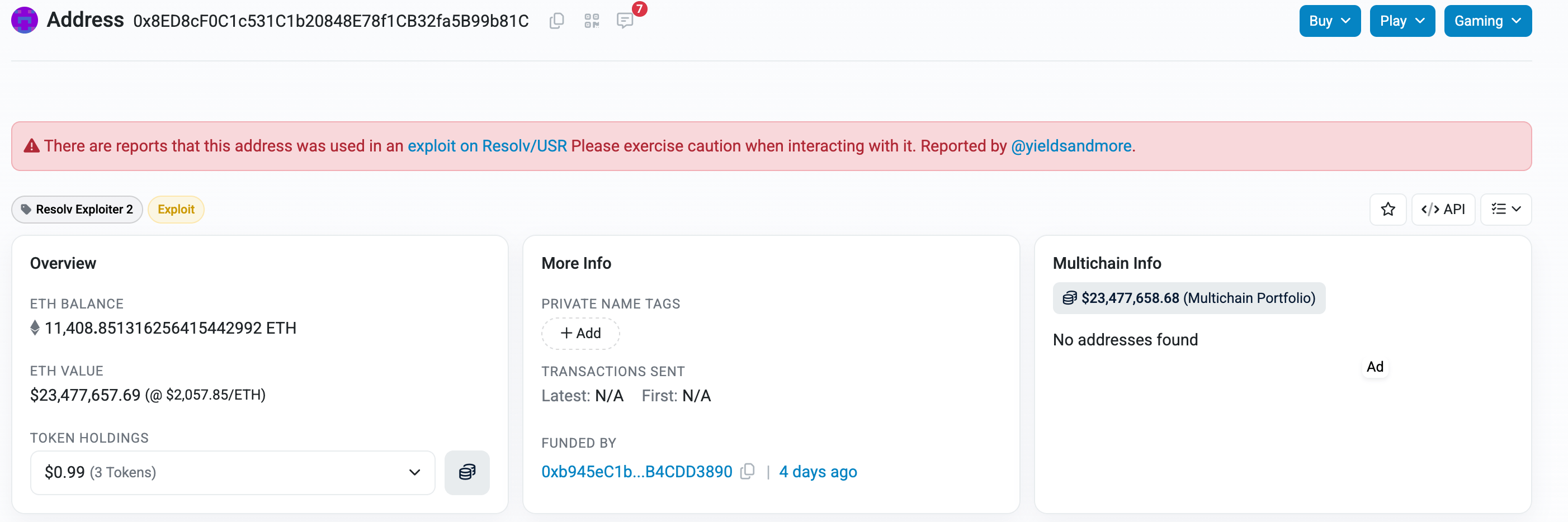
Resolv got absolutely rinsed for $24.5 million. Someone snagged a private key that controlled their USR stablecoin minting process and went wild, creating $80 million worth of unbacked tokens before dumping them for real ETH. The fake coins sent USR from its $1 peg straight down to 26 cents, which is not a good look for a stablecoin.
What's brutal here is that Resolv had done everything "right" - 18 security audits, all the usual precautions. But as Chainalysis pointed out, they got too comfortable trusting off-chain infrastructure. The minting system had no hard limits once that private key was compromised, so the attacker could basically print money until someone noticed. Resolv's trying the "please give us back 90% and we'll let you keep 10%" negotiation, but we’ll see if that works. (read more)
Miscellaneous mattjay
How'd I do this edition?It's hard doing this in a vacuum. Screaming into a void. Feedback is incredibly valuable to make sure I'm making a newsletter you love getting every week. |
Parting Thoughts:
Community was foundational in launching and propelling my career. Community is the only reason I can stand being in Texas during the summer months. Community is the point. Today, I invite you to embrace discomfort on the road to a more vulnerable you.
Stay safe, Matt Johansen
@mattjay