- Vulnerable U
- Posts
- 🎓️ Vulnerable U | #162
🎓️ Vulnerable U | #162
Supply chain pandoras box, claude source code leak, $280M in crypto stolen, Railway was serving up other user's data, and much more!
Read Time: 5 minutes

Brought to you by:
Howdy friends!
Finally home after BSidesSF, RSA, and then all the way to Boston for PAX East. Was a whirlwind but was a lot of fun. Saw a lot of great people. Met a lot of YOU for the first time! Got lots of great feedback, thank you for that.
This week has been taxing. Here is my quick rant if you haven’t been following.
ICYMI
🖊️ Something I wrote: China has now compromised wiretap infrastructure at nine US telecoms AND the FBI
🎧️ Something I heard: Exposing the US Surveillance State ft. Jake Laperruque
🎤 Something I said: The Real Reason Meta is Killing Encrypted DMs?
🔖 Something I read: Vulnerability Research Is Cooked by tqbf
Vulnerable News

What the hell is going on in cybersecurity this week? We’ve got the biggest supply chain hacks back to back to back to back, not even all by the same threat actor. We have npm packages, PyPI packages, Axios pushing malware, claude code leaking source code, Cisco leaking source code. This is what happens when you build the internet on top of underfunded open-source software and then attackers figure out how to exploit the trust built into it.
If you look at the timeline, this starts with Trivy getting popped through GitHub and CI/CD pipeline abuse. Attackers get access to GitHub tokens, they cut malicious releases, and now that malware is getting pushed into environments automatically. From there, it just keeps going: credential harvesting, Docker Hub, npm packages, PyPI packages. LiteLLM becomes a huge jump-off point because it sits in the middle of everything and has access to secrets across multiple environments. At that point, they’re not just stealing data, but are collecting everything they need to keep going.
Now we’re dealing with the fallout. Checkmarx, LiteLLM, Mercor, Cisco: these are all showing up as downstream effects. Attackers are pulling SSH keys, AWS creds, Kubernetes secrets, TLS certs, anything they can get their hands on. Some of this is already being sold, some of it is getting ransomed, and some of it hasn’t even been used yet.
And while all of that is happening, you’ve got a completely separate attack against one of the most widely downloaded npm packages, Axios, by North Korea doing the exact same thing.
Right now, you don’t actually know if you were impacted. Even if you don’t use Axios, something you use probably does. Even if you didn’t touch Trivy, something in your pipeline might have. That’s why this feels so bad. There’s no clean way to scope it. The only move right now is to assume secrets that have touched anything in the GitHub/npm/PyPi ecosystem are compromised and start rotating everything. API keys, tokens, anything tied to GitHub, CI/CD, or environment variables. Attackers are still figuring out what they have, and we’re going to be dealing with this for weeks. (read more here, here, here, here, here, and here!)

Every unauthorized login is a potential breach. Workforce IDV closes that gap by verifying every login is legitimate before granting access.
Download the checklist to evaluate solutions against seven must-have features and build stronger defenses against credential-based attacks. (read more)
*Sponsored
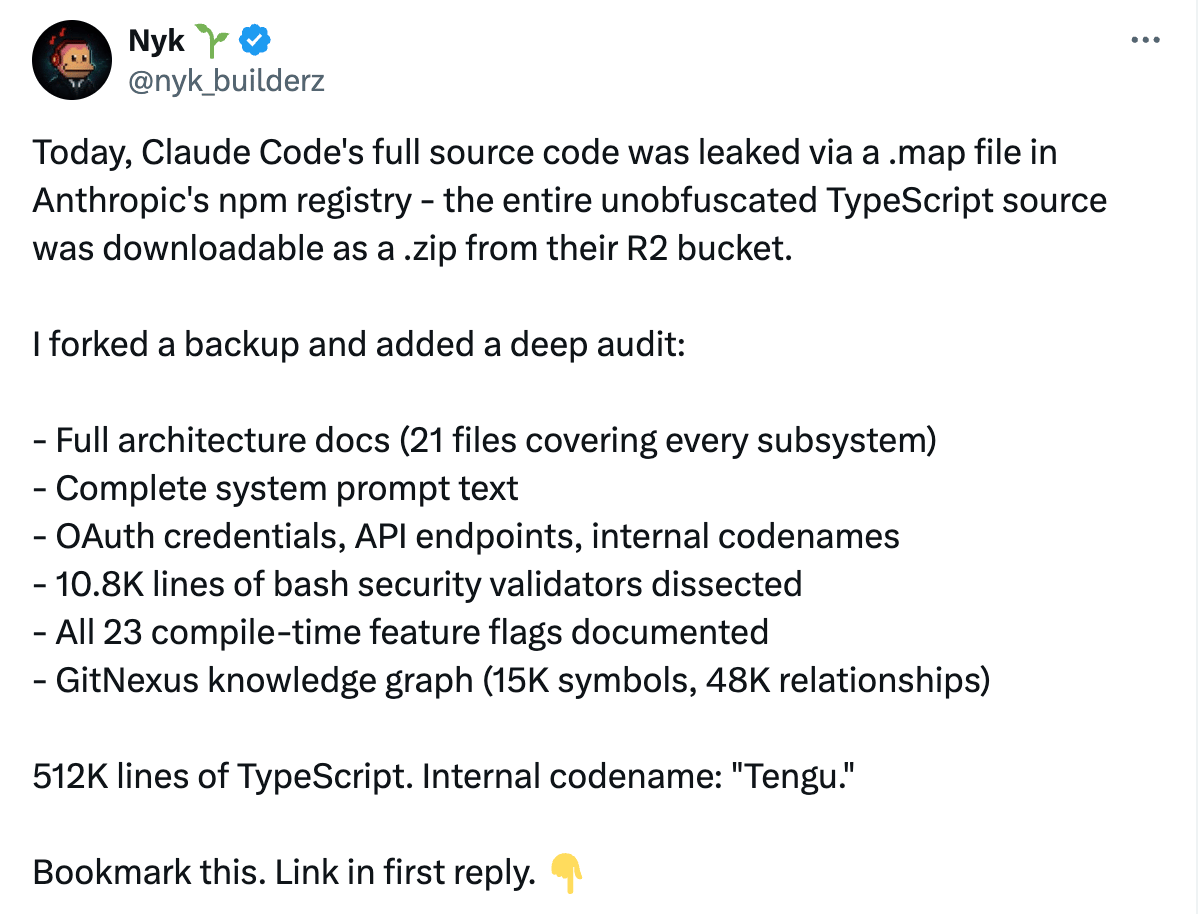
Claude Code source code has been leaked. Not that consequential of a leak, to be honest, but still kind of fun to click around and see all the stuff that's behind the scenes, like hidden flags and unreleased features and things like that. I haven't even wrapped my head around how the leak actually happened via a .map file in their npm registry.
You're going to read a lot of headlines about this. I think the more interesting part is the lessons learned of how they leaked it. People just treat GitHub like it's this walled garden special snowflake kind of place. I think what's happening on Twitter right now is people are feeding the source code leak to Claude to then generate summaries of the things that were leaked in Claude Code, which is a funny, ironic thing.
A few thoughts there: It’s a good practice to not commit secrets to source code. Claude Code is just the front-end app. We are just talking about a very good terminal app at the end of the day. This isn't the models. This isn't a lot of the other stuff. This is just the features and scaffolding around interacting with Claude for the code stuff. (read more)

This report by Beyond Trust covers a critical command injection vulnerability in the Codex cloud environment, which exposed sensitive GitHub credential data. The vulnerability exists within the task creation HTTP request, which allows an attacker to inject arbitrary commands through the GitHub branch name parameter. This can result in the theft of a victim's GitHub user access token: the same token that Codex uses to authenticate with GitHub.
This is not prompt injection. This is much, much, much, much worse. This is a command injection. It's literally executing commands in shell. So your branch name is a string interpreted in bash. No sanitization, no parameterization. So you open a PR with a branch name on a victim GitHub repo. If you're using Codex on that GitHub repo, it goes into Codex land, executes that code, and grabs your OAuth token from your GitHub.
Vulns are back on the menu, boys and girls. (read more)
Railway was super popular a bit ago. It came with your full stack, so you can just deploy all your stuff onto Railway and it would be able to connect to all sorts of other stuff. It's got a lot of other stuff under the hood and will come with everything you need, the connectors, the databases, and so on. It's pretty slick. A lot of people run their apps on it.
Well, Railway done f*cked up. They started showing users’ data to other users. According to the Railway blog, they “experienced an incident where CDN features were accidentally enabled for some domains without users enabling them. For those affected, this may have resulted in potentially authenticated data being served to unauthenticated users. A Railway engineer rolled a change causing HTTP GET responses to be incorrectly cached across some small percent of domains. During this window, cache responses may have been served to users other than the original requester.”
It's basically giving you other users’ information. Authenticated data is served to unauthenticated users, or to authenticated users, just not you. (read more)
There aren't enough hours to process every signal or threat intel that comes your way. Vespyr, Nebulock's autonomous hunting agent, closes the gap between threat intel and actionable detection. It captures intelligence, maps it to your environment, identifies relevant behavioral indicators, and executes the hunt tied to your data, stack, and exposure for contextual security analytics.
*Sponsored
Drift Protocol just got absolutely rinsed for $280 million in what they're calling a "highly sophisticated operation" with weeks of preparation. The attackers managed to take over the platform's security council admin powers through what sounds like some social engineering, then used pre-signed transactions to bypass withdrawal limits. Drift's trying to save face by saying there weren't any bugs in their smart contracts - just that someone got tricked into approving malicious transactions.
Blockchain security firm Elliptic isn't buying the mystery though, and they're pointing straight at North Korea. The attack patterns, laundering methods, and network indicators all match previous DPRK operations. If confirmed, this would be North Korea's 18th crypto heist this year, pushing their 2026 total over $300 million. The tactics apparently mirror last summer's $1.5 billion Bybit hack. (read more)
The FBI officially declared a suspected Chinese hack of its internal surveillance system a "major cyber incident" under FISMA. That's a pretty big deal since agencies rarely make that call, and it means the breach likely compromised significant amounts of sensitive data. We're talking about pen register and trap-and-trace surveillance returns, which is a roadmap of who the FBI is watching and why. The breach happened through a commercial ISP's vendor infrastructure, and the FBI told Congress the affected system also held PII on investigation subjects.
This adds another notch to China's belt alongside Volt Typhoon's infrastructure burrowing and Salt Typhoon's telecom rampage that stole Trump's call records. It's separate from the Iranian hack of FBI Director Patel's personal emails, so the bureau's getting hit from multiple angles. As one official put it, it's "embarrassing" for the FBI to get breached by the same hackers they're supposed to be tracking. (read more)

Apple quietly rolled out another layer of ClickFix protection in macOS Tahoe that's way more sophisticated than what we saw before. This one runs inside XProtect and actually analyzes what you're pasting, not just the behavior. When it spots something nasty, you get a hard "Malware Detected, Paste Blocked" message with zero override options - no "paste anyway" button this time. (Great thread on this here)
It uses the Endpoint Security framework to intercept pastes before they hit terminal apps, extracts URLs and IPs from the text, then checks them against Safari's Safe Browsing Service in real time. It only triggers if the content originally came from a browser (Apple maintains a list of 23 browser signing IDs). It monitors command execution afterward, so if someone tries to obfuscate a malicious domain to slip past the content scanner, XProtect will catch it when the command actually runs and kill the process. Honestly stoked to get more tools against ClickFix which has been WILDLY successful as a technique. (read more)

Apple just pulled a rare move by expanding iOS 18.7.7 security updates to way more devices after the DarkSword exploit kit started making rounds. DarkSword targets iPhones running iOS 18.4 through 18.7 using six different vulnerabilities and deploys some aggressive malware like GhostBlade, GhostKnife, and GhostSaber. Apple had basically abandoned iOS 18 updates for newer devices that could run iOS 26, leaving users who chose to stay on the older OS vulnerable.
Some researcher decided to dump the entire DarkSword exploit kit on GitHub last month, basically handing it to anyone who wanted to target older iPhones. Now Apple's doing damage control by making the security patch available to everything from iPhone XR all the way up to iPhone 16 models. Keep your phones up to date!! (read more)
Another Chrome zero-day that's been getting exploited in the wild - CVE-2026-5281, fourth one Google has had to emergency-patch this year. This one's a use-after-free bug in Dawn, which is Chrome's WebGPU implementation. Attackers can leverage it to crash browsers, corrupt data, or cause other nasty side effects. The fix is rolling out now in Chrome 146.0.7680.178 for desktop users across Windows, macOS, and Linux.
Google's already dealt with three other zero-days since the start of the year, including bugs in CSS font handling, the Skia graphics library, and V8 JavaScript engine. Last year they had to patch eight zero-days total, many discovered by their own Threat Analysis Group. As usual, Google's keeping the exploit details under wraps until most users get patched up. If I get on a Zoom with you and your browser is waiting on an update, I will call you out! (read more)
Miscellaneous mattjay
How'd I do this edition?It's hard doing this in a vacuum. Screaming into a void. Feedback is incredibly valuable to make sure I'm making a newsletter you love getting every week. |
Parting Thoughts:
Community was foundational in launching and propelling my career. Community is the only reason I can stand being in Texas during the summer months. Community is the point. Today, I invite you to embrace discomfort on the road to a more vulnerable you.
Stay safe, Matt Johansen
@mattjay

