- Vulnerable U
- Posts
- 🎓️ Vulnerable U | #163
🎓️ Vulnerable U | #163
Mythos Mega Threat, FBI Cybercrime 2025 stats, Massive crypto heist of over $280 Million, and much more!
Read Time: 9 minutes

Brought to you by:
Howdy friends!
What a couple of weeks! We get back from RSA and the supply chain hacks from hell stacked back to back to back. Then Anthropic decides to break the internet. I’m writing this live on stream now (hi live stream homies!) - we’ve spent the better part of 8 hours talking mostly Mythos and what it means for the future of security. Feel free to check the VODs on my YouTube if you’re curious.
Other than that I hope you all are enjoying your Spring and looking forward to some summer travel. I’m currently loving the weather in Austin and trying to get away from the AI and Cyber hellscape as often as I can (not often).
Let’s get to it!
ICYMI
🖊️ Something I wrote: I was seeing a lot of chatter about Mythos vs Open Models and wanted to get some context and thoughts on paper about it.
🎤 Something I said: Got to hang out with Jcran from Mallory to see what he’s been building around AI and threat intelligence
🔖 Something I read: The full 245 page pdf on mythos - worth going through the actual data the headlines are coming from - And for something a little less Mythos - A Detection Researcher Mindset
Vulnerable News
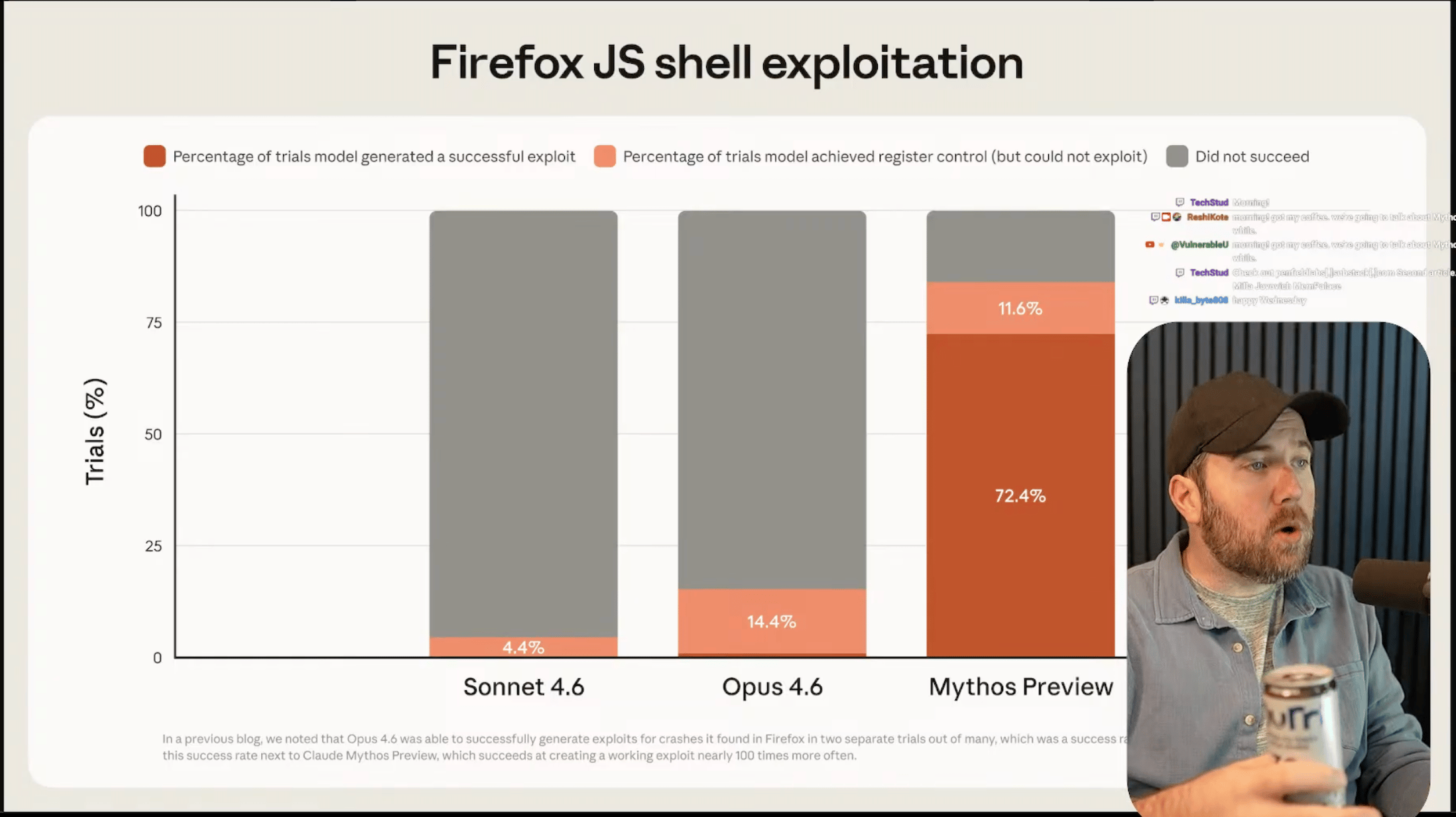
Mythos is here! The internet is doomed! (I’ve spent almost 8 hours on live stream talking about if that is actually true…)
Here is what we actually know - it's been so successful at finding security vulnerabilities that if they released it, they're worried about national security, and the sanctity of the internet in general. They've given the tool to 40 companies they consider critical infrastructure and they're allowing these people to use Mythos to try to find and then subsequently fix all of the vulnerabilities that it would be good at finding before this fallout could possibly happen.
I’ve gotten more hate about this story than anything in a long time on social media. People are absolutely revolting - saying it must just be marketing hype. But let me give you some inside baseball: I've gotten to talk to people who run security for some of the people on this list that are telling me that the claims are real, that they are surprised at the amount and quality of the security vulnerabilities that this thing has been able to find.
Of course Anthropic is incentivized to overhype this. I've been super critical of all of the frontier model companies coming out and being like this thing that we just built is so dangerous. That being said, when we're talking about the ability to find security vulnerabilities, Opus was already getting crazy good at this.
If you want to hear me talk about this for literal hours, check my live stream archive from this week - (specifically here and here) I pull up and react to TONs of hype and criticism of Mythos and talk about where I think this is all going. (read more)
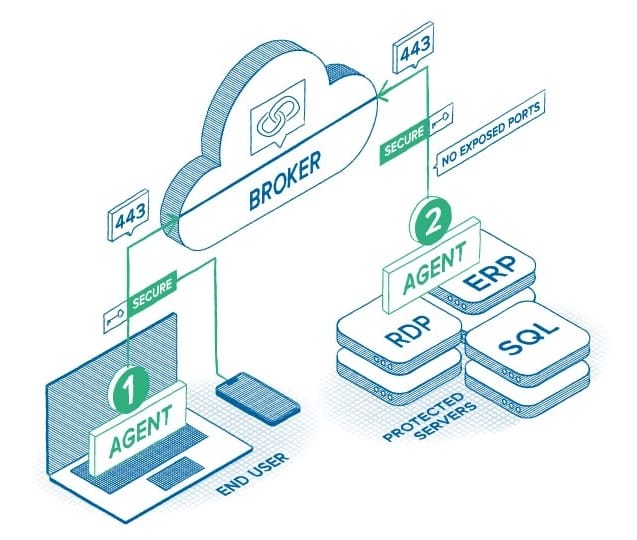
ThreatLocker Zero Trust Network Access reduces your attack surface by removing unnecessary access pathways. Users are granted access only to specific applications—not entire networks—based on strict policy controls. With every connection verified and enforced in real time, organizations gain stronger control over access and eliminate the risk of overexposure.
*Sponsored
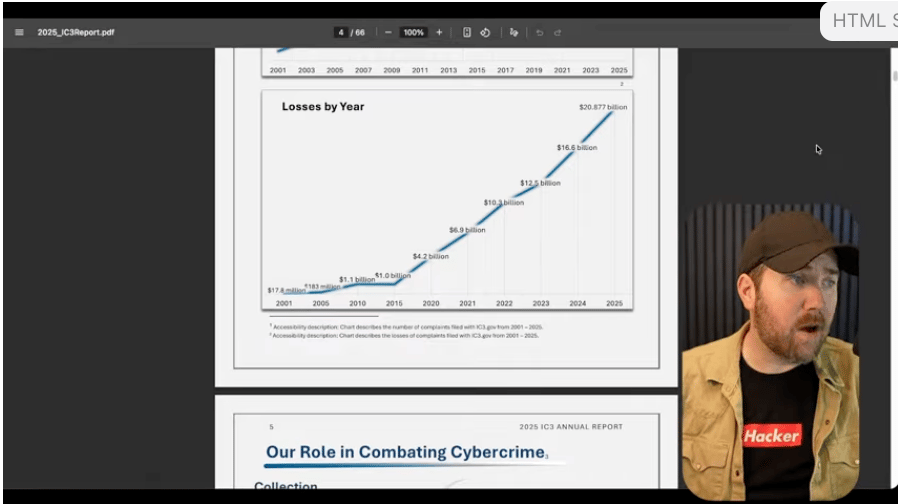
(click the pic to get brought to the timestamp in live stream when I talk about this report)
The Internet Crime Complaint Center, otherwise known as IC3, put out their yearly report and it's always staggering. The number of complaints per year is just straight up and to the right, and the losses are people who lost stuff in cyberattacks, scams, whatever it is, and actually called and reported it, which is not everyone, by any means. It's always old people losing the most.
Investment-related fraud was once again the largest component, and crypto is clearly included in this. Crypto fraud is way, way, way more prevalent than anything else going on: 7.2 billion of the 8 billion in investment scams involved crypto. The scammers initiate contact, show fake profits, hit victims with taxes and fees, and then hit them again with recovery scams. You're hitting vulnerable people at a vulnerable time with the right script and they're just toast.
Education is rarely stopping a lot of security breaches, so why is this possible? We need systemic guard rails that make it really hard for people to do that. Sextortion skews super young, a lot of people wind up committing suicide, and that is another stat that should be talked about. Threats of violence are skyrocketing, crypto investment scams have doubled. The other trends in this report are super interesting as well. (read more)
This one was crazy. This $280 million crypto theft was a six-month-long op. Drift experienced a structured intelligence operation that required organizational backing, significant resources, and months of deliberate prep. Contributors were approached in person at conferences, engaged across multiple countries, and worked with what appeared to be a legitimate trading firm that built trust over half a year.
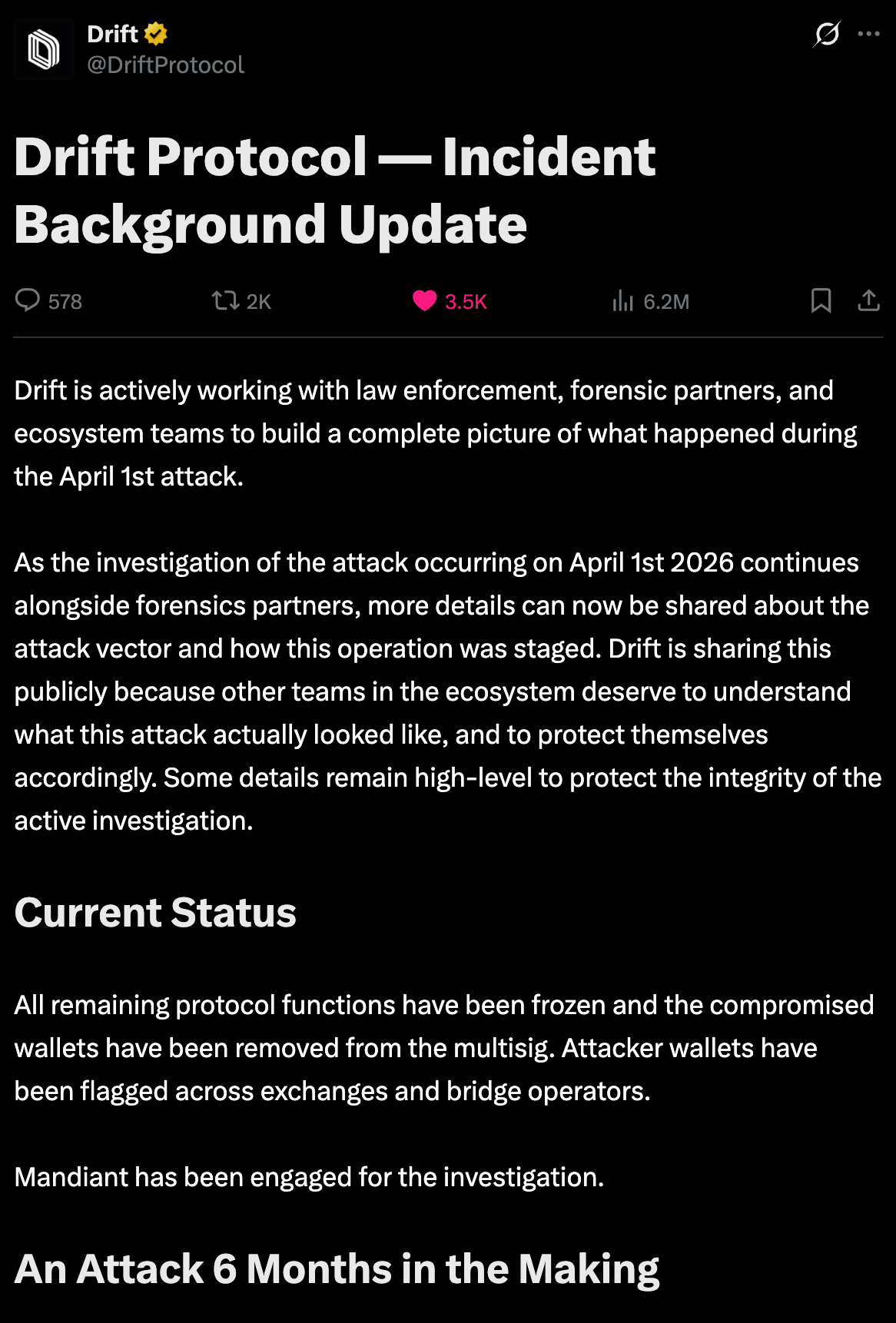
(click pic for link to full article)
They onboarded a vault, deposited over a million dollars of their own capital, and built a functioning operational presence inside the ecosystem. They felt like co-workers at this point. But when the hack happened - it should all look familiar. Malicious GitHub repos exploiting VS Code vulnerabilities, fake TestFlight wallet apps, and months of social engineering that made these actions feel completely normal.
On April 1st, in 12 minutes, $285 million. Boom. The attackers wiped chats, scrubbed evidence, and disappeared. The individuals they met in person were not North Korean nationals, but intermediaries used to build trust. This wasn’t someone you just met online. This was six months of real-world interaction before the rug was pulled. (read more)
(click pic for timestamp of livestream about comfyui)
Censys put out this bit of research about ComfyUI, which is a wrapper around AI image generation tools, widely used and frequently exposed to the internet without authentication. Over a thousand instances are visible, and from an attacker perspective this is an attractive target because the same GPU used for image generation can be repurposed for crypto mining.
Once a ComfyUI instance is identified, the tool attempts to execute attacker controlled code through the custom node ecosystem. Some nodes accept raw Python code and execute it, effectively turning it into remote code execution as a service. How nice of them. You have a system exposed to the internet that runs arbitrary Python and has access to GPUs. From there it’s persistence and mining. (read more)
Most “AI for security” stops at summaries and dashboards. Tenable Hexa AI goes further as an agentic engine inside Tenable One, orchestrating agents and humans to automate asset tagging, risk reprioritization, coverage, and reporting. It turns exposure intelligence into coordinated action at machine speed, while security teams stay firmly in control.
*Sponsored
(click pic for livestream timestamp about fortinet)
Fortinet released an emergency software update to address an actively exploited vulnerability in FortiClient EMS, an endpoint management tool for customer devices. Unknown attackers were first observed attempting to exploit the vulnerability in March, and exploitation has already ramped up with growing attacker interest and broader targeting.
Best time to apply the hotfix was yesterday. Otherwise, right now. Federal agencies have until April 9th to remediate. NHS England has already issued a high severity alert and said it is almost certain there will be further exploitation in the immediate future. Compromise of an EMS server can provide a path to multiple managed endpoints, making this attractive to ransomware operators and espionage actors. (read more)
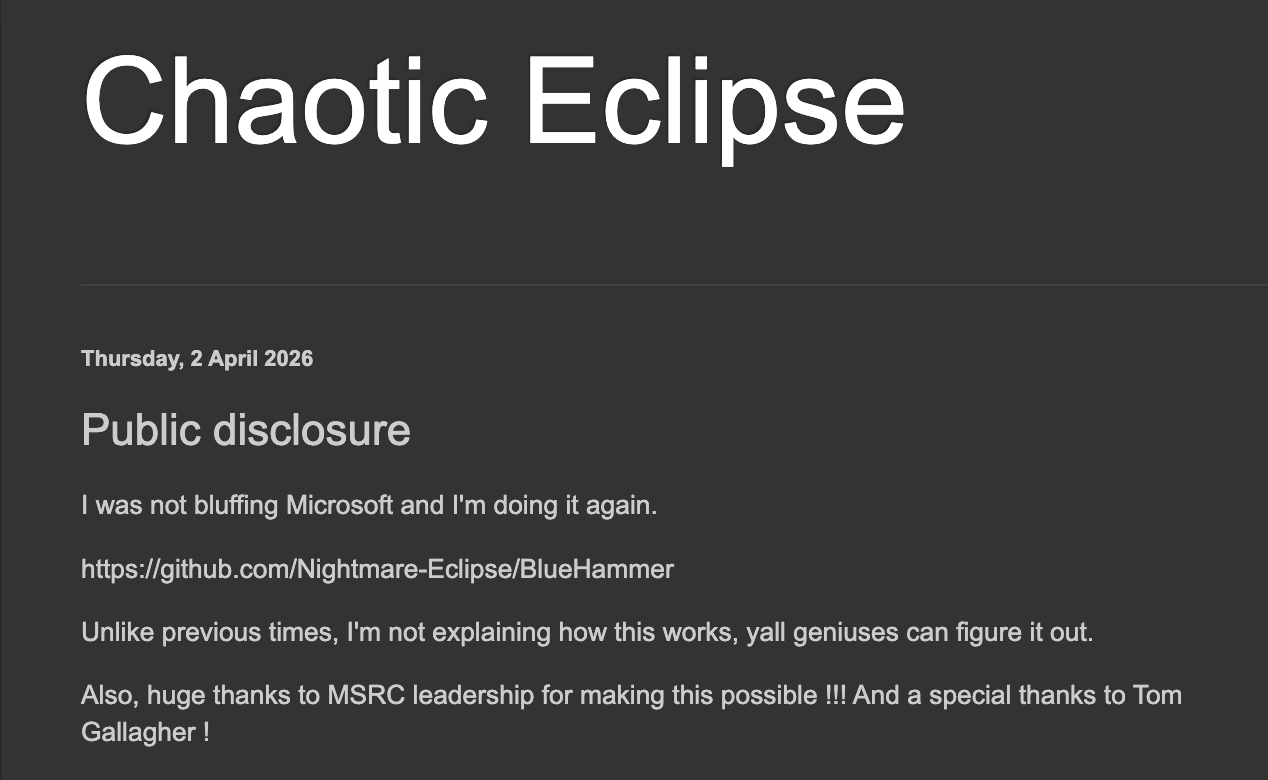
A security researcher just dropped raw exploit code for an unpatched Windows privilege escalation flaw dubbed BlueHammer. No official patch, no update, and the flaw is considered a zero day. The researcher was unhappy with how the disclosure process was handled and just pushed the exploit out publicly.
“I'm not bluffing Microsoft. I'm doing it again. I'm not explaining how this works. Y'all geniuses can figure it out. GitHub exploit code, that's it.” Some people couldn’t get the exploit to work, the researcher is just kind of over this whole bug and doesn’t care to make the PoC more stable. It’s not the craziest vuln, but it is still interesting to see us deal with public disclosure in 2026 like this. (read more)
As stated earlier in the IC3 FBI data report - Crypto scams are a huge multi billion dollar industry every year. I usually go so far as to say the only purpose for crypto is to fascilitate crime and scams. Ransomware isn’t really asking for duffel bags of unmarked bills under a park bench… So! I’m glad to see this information sharing effort take shape as it is long overdue. They're offering the same cybersecurity intel they share with traditional banks to eligible crypto firms.
While Treasury's extending a helping hand to crypto companies, the Trump administration just proposed slashing $707 million from CISA's budget, specifically targeting "external engagement offices" that do exactly this kind of threat sharing with other industries. So we're getting more crypto-focused cybersecurity cooperation while cutting broader private sector programs. (read more)
Google's threat intel sharing info on UNC6783, a financially motivated threat actor that goes by “Mr. Raccoon.” Instead of going directly after big companies, they're compromising the business process outsourcing (BPO) providers that handle customer support for these firms. Once they're in, they're making off with Zendesk support tickets containing all sorts of corporate data, then turning around and extorting the original targets.
They'll social engineer support staff through live chat, directing them to spoofed Okta login pages that follow specific patterns like "company.zendesk-support##.com." What makes it nastier is their phishing kit can steal clipboard contents to bypass MFA. The group also recently stole 13 million support tickets from Adobe after compromising an Indian BPO. Google's recommending FIDO2 keys and monitoring live chat for suspicious activity, but honestly, if your BPO gets owned, you're going to have a bad time regardless. (read more)
The FBI just pulled off another router takedown, this time kicking APT28 (aka Fancy Bear, those GRU folks) off over 18,000 compromised TP-Link routers worldwide. What was super interesting to me on this one was how the attack worked - instead of dropping malware on individual devices, the Russians just changed DNS settings on home and small office routers. That meant every device connecting to those Wi-Fi networks automatically got redirected through malicious infrastructure, giving the GRU "tremendous access" to traffic from 200+ organizations.
The FBI's Brett Leatherman called it uniquely contagious because compromising one router immediately compromised every connected device in that network. This marks the latest in a series of router disruptions dating back to 2018, with the FBI evolving from just sinkholing domains to actively cleaning infected devices and blocking reinfection. (read more)
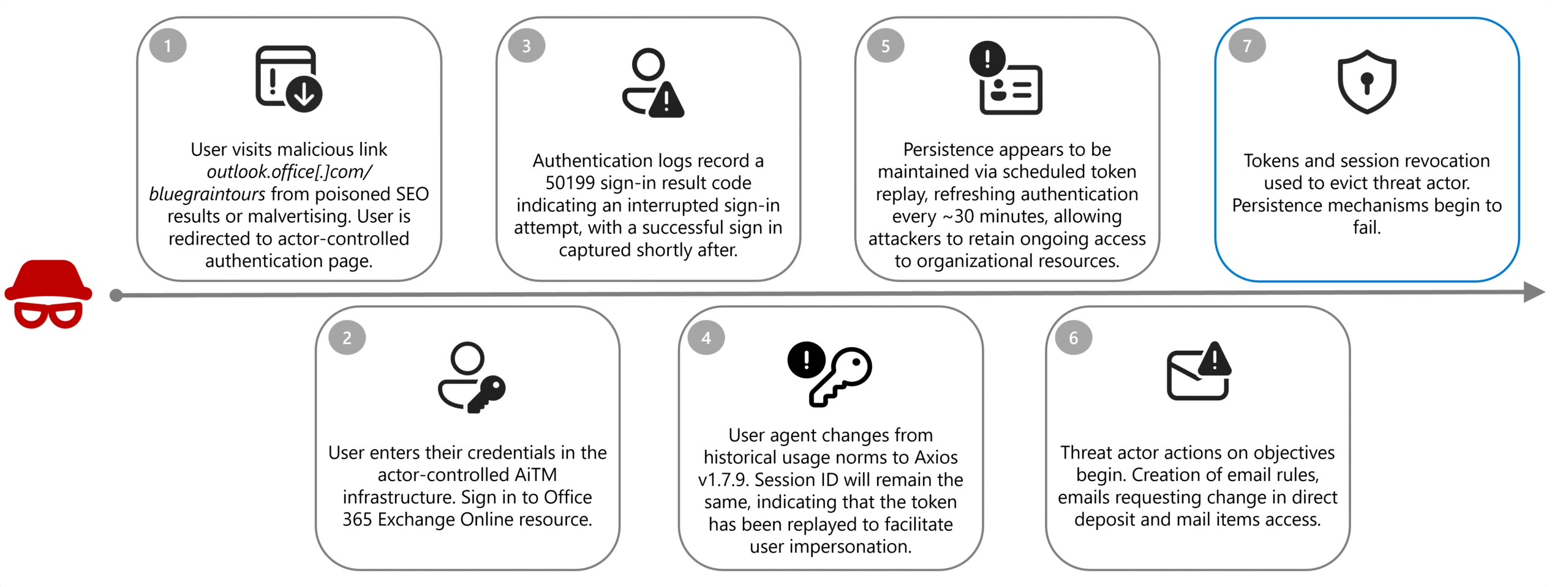
Payroll pirates are using SEO poisoning and malvertising to trick people into fake Office 365 login pages, then leveraging adversary-in-the-middle attacks to steal session tokens and bypass MFA. Once they're in, they search for HR and payroll contacts, create sneaky inbox rules to hide their activities, and email HR pretending to be the employee asking to change direct deposit info.
We even got targeted by this at Vulnerable U! Minus the HR compromise, just some good old fashioned spear phishing to the people on my team the attackers thought did payroll. (read more)
Miscellaneous mattjay
How'd I do this edition?It's hard doing this in a vacuum. Screaming into a void. Feedback is incredibly valuable to make sure I'm making a newsletter you love getting every week. |
Parting Thoughts:
Community was foundational in launching and propelling my career. Community is the only reason I can stand being in Texas during the summer months. Community is the point. Today, I invite you to embrace discomfort on the road to a more vulnerable you.
Stay safe, Matt Johansen
@mattjay