- Vulnerable U
- Posts
- 🎓️ Vulnerable U | #164
🎓️ Vulnerable U | #164
Claude Mythos! What do we need to know? Adobe, Microsoft and wolfSSL 0 days, major crypto breaches, and much more!
Read Time: 9 minutes

Brought to you by:
Howdy friends!
Mythos!!11
Ok, now that we got that out of our system. How are we all hanging in this week? Tech news is moving at a break neck pace lately. Hopefully I’m helping you keep above water and cutting through the noise.
In case you missed it, I’ve been live streaming on YouTube and Twitch 3 days a week for 3-4 hours each shot in the mornings (tue, wed, thu) - come hang.
ICYMI
🖊️ Something I wrote: My predictions on Opus 4.7 (early signs point to true)
🎧️ Something I heard: Watched the CISO of Google say their goal is to eliminate all software vulnerabilities in the world…
🎤 Something I said: My thoughts on Mythos and what you need to do about it
🔖 Something I read: Anthropic gave defenders a playbook. The Last Mile Is Missing.
Vulnerable News

I’m reading this Cloud Security Alliance report because a lot of really smart people saw Mythos and said we can’t sit on the sidelines anymore. At a high level, the guidance is simple: use LLMs for vulnerability discovery and remediation, accelerate your teams with coding agents, and prepare for more incidents. None of that is new, but if you’re not doing it already, you’re behind. And yeah, prepare for burnout. That was true long before Mythos.
What’s actually changing is the speed and capability. Time-to-exploitation is collapsing, we’re talking same-day weaponization now. But the bigger shift is in complex exploit chains. The kind of vulnerabilities that used to require a small number of elite researchers, tens or maybe hundreds of people, are starting to become more accessible. That’s the part that matters, not the hype about a “super hacker.”
I’m not treating Mythos as a one-off. If Anthropic proved this is possible, then it’s going to show up everywhere else.
That’s the real takeaway: we’re on a clock.
Whether it’s months or a year, this capability is going to spread, including to nation-state actors with unlimited resources. I’m taking the marketing with a grain of salt, but the people actually using these systems are telling me they’re finding real vulnerabilities at scale and running incidents on them right now.
At the same time, Mythos isn’t going to find every vulnerability in everything. What it looks really good at right now is old code, especially memory bugs in C, and that alone is a big deal because that code underpins so much of what we rely on. The opportunity is to use that capability on defense, find and fix faster than attackers can. But either way, this is a race, and the organizations that build the muscle now, process, tooling, and culture, are the ones that will keep up. (read more)

I’m joining Push Security’s new research webinar series, State of Browser Attacks, and the guest lineup alone makes it worth your time. We’re talking Troy Hunt, John Hammond, and Push’s own research team all in one place.
The browser has quietly become the most dangerous surface in modern attacks. Just this year we’ve seen ClickFix variants everywhere, phishing campaigns hijacking search engine results, and device code phishing scaled up by brand new PhaaS kits. And we’re barely into Q2.
This series breaks it down simply so you know exactly what to watch for and how to respond.
Register your spot and see you there!
*Sponsored

Kraken says it’s dealing with an active effort by threat actors to recruit insiders at crypto companies, gaming companies and telecoms, especially through third-party contractors and BPOs.
This is something that keeps happening. Either weak processes let someone get socially engineered into resetting access, or someone just got bribed. That’s exactly what this looks like. They got access to about 2,000 accounts’ worth of data: balances, account info, wallet IDs, the kind of data you use to figure out who to target next.
Once that access was used, the extortion started. They got video evidence of what the help desk employee could see, be it screen recordings or something else, and tried to cash in. Kraken didn’t pay and is working with law enforcement, and thinks it can track these people down. That’s the right move, but the bigger issue is how this keeps happening in the first place.
If you haven’t locked this down, I’d argue this is security team priority number 1 because so many threat actors are doing this. (read more)
I saw a ton of buzz this week around the FBI being able to read Signal messages, and every time this comes up, it’s the same reaction: “Signal is broken.” I get flooded with DMs saying exactly that.
But Signal is not broken. It’s still the pinnacle of end-to-end encryption. It’s open source, it’s implemented correctly, and it does exactly what it’s supposed to do.
What actually happened here is simple: they had an end. End-to-end encryption protects messages in transit, not once they hit the device. The endpoint is your phone. If someone has your phone, they have the end. At that point, there’s nothing to “break.” The message was encrypted all the way to the endpoint, and the endpoint is compromised.
The interesting part is how they were still able to read messages even after the app was deleted. That points to data being stored elsewhere on the device, like in the notification log or push notification database. That’s where message content can still exist, outside of the app itself. That’s worth understanding, because most people don’t realize that’s happening. (read more)
OpenAI is rotating its macOS signing certificates and forcing app updates after getting caught in the Axios supply chain attack from late March. The good news is they say no user data or systems were actually compromised. The bad news, and why they’re being overly cautions, is their GitHub workflow downloaded a malicious version of Axios after North Korean hackers (UNC1069) social-engineered the lead maintainer and hijacked his accounts. The malicious code was only live for three hours, but given that Axios pulls over 100 million weekly downloads, the blast radius was massive.
OpenAI believes the timing and setup of their workflow likely prevented the certificate from being stolen, but they're treating it as compromised and revoking it by May 8. If you're running their macOS apps, update now or they'll stop working. The root cause was a misconfigured GitHub workflow, which they've since fixed. (read more)
One Breach Got Exaggerated. The Other Dumped a Full Movie Online

I saw a lot of hype around the Rockstar Games breach, especially claims that anti-cheat source code was stolen. That got walked back pretty quickly. What actually appears to have been compromised is Snowflake analytics data: things like in-game revenue, purchase metrics, player behavior and support analytics. Rockstar confirmed a breach but said it was limited and non-material, with no impact on players.
This looks like one of those BPO-style exposures, basically whatever data that third-party environment had access to. Not great, but not the catastrophic “source code leak” people were throwing around on Twitter. A good reminder that early breach narratives are almost always wrong.
The other story is way messier: A hacker group leaked full HD clips and now the entire unreleased Avatar movie is online after an apparent extortion attempt failed. This isn’t rough cuts or unfinished footage. This is fully produced content, just out on the internet months before release. No official word yet, but this is a bad look, and it likely came down to the same thing we keep seeing: compromised employee access, probably via phishing or social engineering. (read more here and here)

This story from Kim Zetter is wild: You’ve got a top executive at Trenchant, Peter Joseph Williams, who had everything and still decided to steal and sell zero-days to a Russian broker. He says he was dealing with anxiety, burnout, depression, and financial pressure. His attorney calls it an “extraordinarily poor judgment” period. But at the end of the day, he signed deals worth up to $4 million to sell eight hacking tools, including some incredibly powerful exploits, to a broker tied to the Russian government.
The mental health angle matters, but it doesn’t explain this away. He admits depression and burnout weren’t the cause. Prosecutors are pretty clear: this was about lifestyle. He was making serious money already, millions in salary, and still chasing more. Luxury cars, expensive travel, jewelry, a $1.5 million house. He pulled in about $1.3 million from the deal on top of everything else.
What makes this even crazier is how brazen it was. He wasn’t recruited, he reached out to the Russian buyer himself. He created an anonymous email account and started the relationship. While the FBI was investigating, he kept selling. While the company was investigating, he was put in charge and let a subordinate take the fall for his own actions. He was literally sitting in meetings with federal agents while continuing the crime. Next-level recklessness.
Prosecutors say the exploits could potentially access millions of devices worldwide. By selling them, he may have handed adversaries the ability to target the U.S., Australia, and allies. It’s a reminder that sometimes the biggest risk isn’t the external attacker, but the person who already has the keys. (read more)
What year is it?! Adobe just patched a zero-day (CVE-2026-34621) that hackers have been exploiting for at least four months. The bug hits Acrobat DC, Reader DC, and Acrobat 2024 on both Windows and macOS, letting attackers drop malware on your system just by getting you to open a rigged PDF file. Security researcher Haifei Li caught this one when someone uploaded a malicious PDF to his scanner - the first sample showed up on VirusTotal back in November. (read more)
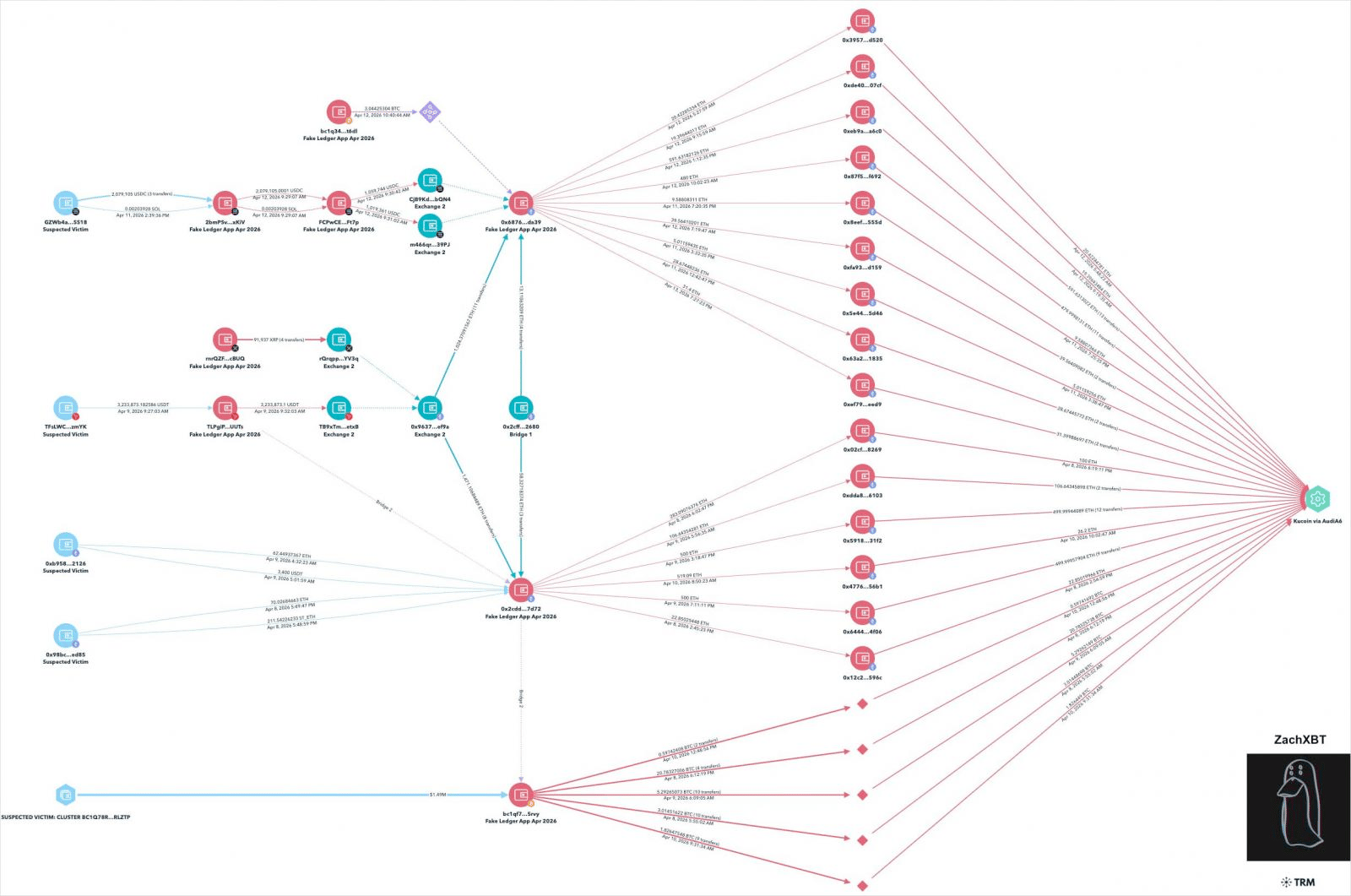
A fake Ledger Live app made it through Apple's App Store review and proceeded to drain $9.5 million in crypto from 50 people over just a few days in early April. Users downloaded what they thought was the legit Ledger app, entered their seed phrases, and watched their wallets get emptied across Bitcoin, Ethereum, Solana, and other chains. Three victims alone lost over $1 million each, with musician G. Love (who? I’m old.) getting hit for $430k in BTC.
Apple's since pulled the app, and KuCoin froze the accounts receiving the stolen funds. Though that freeze expires April 20th unless law enforcement steps in. Worth noting: Ledger doesn't actually offer a macOS app through the App Store, only on their website, which is exactly the gap these scammers exploited. They pulled a similar stunt on the Microsoft Store back in 2023 for $768k, so this playbook isn't new. (read more)
RedSun, BlueHammer, and Microsoft 0-day drama

This one has just been kind of amusing. Disgruntled security researcher just painfully dropping 0-days publicly because he wasn’t happy with Microsoft bug bounty response.
But now we’re seeing some exploit activity via Huntress. John Hammond’s research on this is dropping in the AM - I have an embargoed link but timing won’t work out to include it in this email. LowLevel did a good video on it before we saw the exploit traffic. Keep an eye on this one.
Australia's social media ban for under-16s is turning out to be more of a suggestion than an actual barrier. New research from the Molly Rose Foundation found that 61% of Australian kids aged 12-15 are still accessing their accounts on TikTok, Instagram, and YouTube just fine and they're not even using workarounds. The platforms simply haven't identified or removed their accounts in the first place.
I go into depth about my feelings on Age Verification systems in this video here.
The UK is running pilot programs through May, France's Senate just voted on an under-15 ban, and Greece, Spain, and the Netherlands have all announced similar restrictions coming soon. The Molly Rose Foundation is pushing back, arguing that the UK should ditch the ban approach and instead strengthen its Online Safety Act with actual enforcement mechanisms that make platforms responsible for age verification and content safety. (read more)
A critical vulnerability in wolfSSL (CVE-2026-5194) lets attackers bypass certificate verification by exploiting weak hash validation in ECDSA and other signature algorithms. The flaw basically allows forged certificates with smaller-than-allowed digests to pass verification checks, which could let malicious servers masquerade as legitimate ones. After OpenSSL this is the biggest footprint library of it’s type with 5 billion devices worldwide, including IoT, industrial control systems, and even aerospace and military equipment.
The fix landed in wolfSSL 5.9.1 on April 8, so if you're running anything with wolfSSL baked in, time to check your version. Many devices don't use upstream wolfSSL directly, but they get it through vendor firmware or embedded SDKs, so you'll need to chase down vendor-specific advisories. Props to Nicholas Carlini at Anthropic for catching this one - presumably using Claude super secret hacking tools. (read more)
Miscellaneous mattjay



How'd I do this edition?It's hard doing this in a vacuum. Screaming into a void. Feedback is incredibly valuable to make sure I'm making a newsletter you love getting every week. |
Parting Thoughts:
Community was foundational in launching and propelling my career. Community is the only reason I can stand being in Texas during the summer months. Community is the point. Today, I invite you to embrace discomfort on the road to a more vulnerable you.
Stay safe, Matt Johansen
@mattjay
