- Vulnerable U
- Posts
- Fortinet Customers Confront Actively Exploited Zero-Day, With a Full Patch Still Pending
Fortinet Customers Confront Actively Exploited Zero-Day, With a Full Patch Still Pending

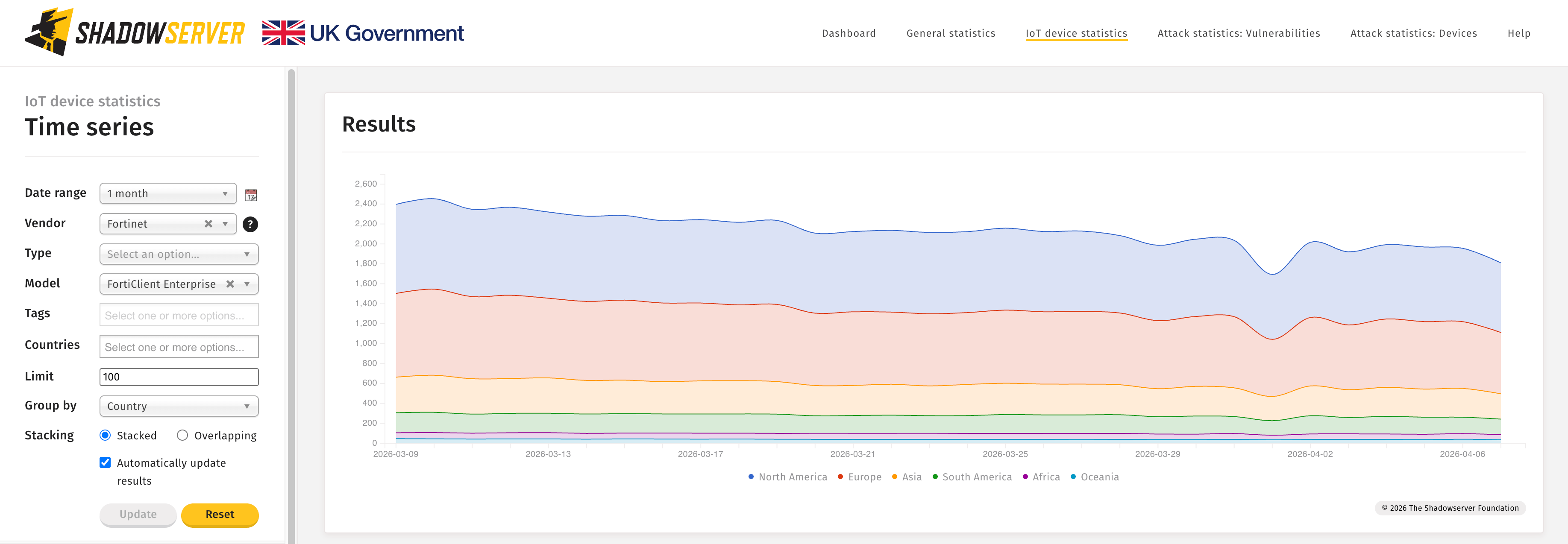
Fortinet released an emergency software update to address an actively exploited vulnerability in FortiClient EMS, an endpoint management tool for customer devices. Unknown attackers were first seen trying to exploit the vulnerability in March, and exploitation has already ramped up with growing attacker interest and broader targeting.
Best time to apply the hotfix was yesterday. Otherwise, right now.
Federal agencies have until April 9th to remediate. NHS England has already issued a high-severity alert and said it is almost certain there will be further exploitation in the immediate future. Compromise of an EMS server can provide a path to multiple managed endpoints, making this attractive to ransomware operators and espionage actors. This is endpoint management software with remotely exploitable code.
Fortinet gave this a severity rating of 9.1 out of 10. Tenable calls it a 9.8, reflecting the fact that the attack can be carried out remotely.
Who remembers the Stryker vulnerability that we just talked about where someone compromised Intune, which is endpoint management software, and compromised it by compromising the admin?
If Fortinet is running this endpoint management software and it has remotely exploitable code, then those who recall the Stryker attack will understand how serious this Fortinet security hole is.