- Vulnerable U
- Posts
- 🎓️ Vulnerable U | #144
🎓️ Vulnerable U | #144
Read Time: 11 minutes

Brought to you by:
Howdy friends!
Happy Thanksgiving! Super thankful for all of you and your continued support that lets me do this for a living. Thankful for anyone who helped along the way to give me a push to keep going when I wanted to stop.
I’m writing this a few hours earlier than normal so I can enjoy Thanksgiving with my family, so apologies if some MASSIVE news comes out Thursday night. There is still a ton of news to cover this week, so lets get to it. No rest for the wicked!
ICYMI
🖊️ Something I wrote: The "AI vs. AI" Fallacy. The narrative that you need "AI defense" to stop "AI attackers" is marketing.
🎧️ Something I heard: Linus Tech Tips going over GrapheneOS phone - Maybe This Phone ISN’T Just for Criminals - Trying Graphene OS for a Month.
🎤 Something I said: this is not how threat intel works… - my thoughts on the Anthropic “intel” report about China using Claude Code to hack 30 companies.
🔖 Something I read: I cosign this open letter! Hacklore, or all the stuff we need to stop getting people worried about like Public WiFi and QR codes.
Vulnerable News
The best named worm ever, Shai-Hulud, is back with a vengeance, hitting over 834 npm packages from major players like PostHog, Zapier, AsyncAPI, Postman, and ENS Domains. The malware uses a two-stage loader that silently downloads the Bun runtime and executes a massive obfuscated payload in the background while your package installs normally. What makes this particularly nasty is its self-healing capability: it searches GitHub for a specific beacon phrase to re-establish command and control if its infrastructure gets taken down.
The attack chain is …fun. On GitHub Actions runners, it escalates to root privileges through Docker manipulation, then goes bananas - stealing credentials from AWS, GCP, Azure, and GitHub, running TruffleHog to scan for hardcoded secrets, and even mining NPM tokens from workflow metadata. If it finds valid NPM tokens, it becomes a worm, automatically poisoning more packages by bumping patch versions. And if all else fails it nukes your entire home directory with a little file shredding. PostHog's already published a detailed postmortem showing how their GitHub Actions workflow got exploited as the initial attack vector, so definitely worth checking your CI/CD security posture. (read more)
I really enjoyed this report that Dropzone AI put out in partnership with the Cloud Security Alliance (CSA) - This is as close to a scientific experiment as you can get for this sort of thing. They timed and measured accuracy of a bunch of analysts responding to some AWS or Azure incidents with and without their AI agent help.
*Sponsored
Mixpanel got hit by a SMS phishing campaign (i hate calling it smishing) and it's rippled out to affect some of their big-name customers, including OpenAI. The analytics company detected the breach on November 8th and did all the standard incident response stuff - locked down accounts, rotated credentials, brought in forensics experts. OpenAI found out they were caught up in this when Mixpanel shared the compromised dataset with them on November 25th.
For OpenAI users, this wasn't a direct breach of their systems. The exposed data was included names, email addresses, rough location data, browser info, and API account metadata. No chat logs, API requests, passwords, or payment details got leaked. My question is why was that kind of personal info even shared with Mixpanel? Not the biggest deal breach in terms of info, just seems unnecessary. OpenAI immediately terminated their Mixpanel contract and said they’re doing security reviews across their entire vendor ecosystem.
Mixpanel’s disclosure is worth reading too: https://mixpanel.com/blog/sms-security-incident/ (read more)
What started as Salesforce warning about "unusual activity" affecting 3 customers has now expanded to a "larger list" (though their CEO insists it's still just "a handful"). ShinyHunters claimed responsibility for the breach, and it's caused a domino effect with other companies like Zendesk, Gong.io, and HubSpot temporarily cutting their Gainsight integrations out of caution. The attackers were apparently doing reconnaissance since October and used some creative user agent strings that they'd previously deployed in other breaches.
This whole thing is also tied to the Salesforce Drift breach AND the CrowdStrike insider risk going on. This threat actor group is prolific and all over the place. I did a video that started about the CrowdStrike insider but turned into a “well these attackers are going to do anything to get your OAuth tokens” - breaching salesforce apps, paying insiders, social engineering helpdesk, SMS phishing, basically anything but traditional exploits, because why bother. (read more)
I’ve been talking about NK cooking both sides of the job market for a bit now. Both getting hired as remote IT workers, but also setting up fake interviews and infecting the job seekers with malware. This is a good rundown of the latter. These researchers mapped out the "Contagious Interview" crew’s stack. Tracing a malicious npm package called "tailwind-magic" back to a Vercel staging server and a GitHub account with 18 repositories. Since October, they've pushed 197 more malicious packages targeting crypto and Web3 developers with fake job interviews.

The OtterCookie payload is pretty nasty - it does all the normal stuff like keylogging, clipboard theft, and multi-monitor screenshots, but it's specifically tuned for crypto theft. It targets browser wallets across Chrome and Brave, hunts for seed phrases and wallet files, and even gives the attackers a remote shell. They're typosquatting legitimate packages like "tailwind-merge" and embedding them in fake DEX projects that look totally legit. Even after taking down the GitHub account, new ones keep popping up weekly. These guys have turned npm into their personal malware delivery service. (read more)
CrowdStrike caught and fired an insider who was leaking internal screenshots to a hacking group. While the threat actors tried to spin this as a successful hack of CrowdStrike's network, the company confirmed it was just a rogue employee sharing access. The hacker never actually got access and this is all somehow related to the Salesforce app (Drift and Gainsight) breaches lately. I go into more in the video. (read more)
Oh you mean that “threat intel” report that felt more like marketing - but also just was a whole lot of info about Claude guardrails failing? That caught some heat?! No way. If you missed it, Congress wants Anthropic's CEO on the hot seat after Chinese hackers turned Claude into their personal cyber assistant. The House Homeland Security Committee is calling Dario Amodei to testify on December 17th about a campaign that hit at least 30 organizations worldwide, using the AI to automate parts of their operations. They're calling it a "significant inflection point" - basically acknowledging that we've crossed into new territory where state actors are weaponizing commercial AI tools at scale.
The hearing lineup is telling - they're also bringing in Google Cloud's CEO and Quantum Xchange's head to talk about how AI, quantum computing, and cloud infrastructure are reshaping the national threats. The committee's worried about adversaries pairing AI-enabled attacks with emerging quantum capabilities to break current crypto protections. (read more)
The House Energy and Commerce Committee just dropped their own version of KOSA, and they've made some significant changes. The big difference is they ditched the "duty of care" provision that would've made tech companies legally liable for social harms to kids. That was the sticking point that killed the Senate version in the House - leadership got spooked about free speech implications. Instead, they're going with softer language requiring platforms to have "reasonable policies, practices, and procedures" to address stuff like violence threats, sexual exploitation, and drug sales.
This is just one of 19 bills they're pushing through committee hearings, including the App Store Accountability Act (which basically federalizes existing state laws requiring age verification) and COPPA 2.0 (extending privacy protections to kids under 17 instead of just 13). You've got grieving parents and senators like Blackburn and Blumenthal on one side pushing hard, while Big Tech's been lobbying against these regulations for years. The watered-down approach might actually have better chances of passing, but whether it'll be effective enough to satisfy the families who've been fighting for this is another question entirely. (read more)
Brian Krebs just pulled off another masterclass, tracking down "Rey" - one of the main admins behind Scattered LAPSUS$ Hunters, the group that's been extorting major companies all year. Turns out Rey is actually Saif Al-Din Khader, a 15-year-old kid from Jordan whose dad flies for Royal Jordanian Airlines. The investigation unraveled after Rey made some opsec fails, including posting a screenshot of a sextortion email that exposed his unique password, which led Krebs down a rabbit hole through breach databases and old forum posts.
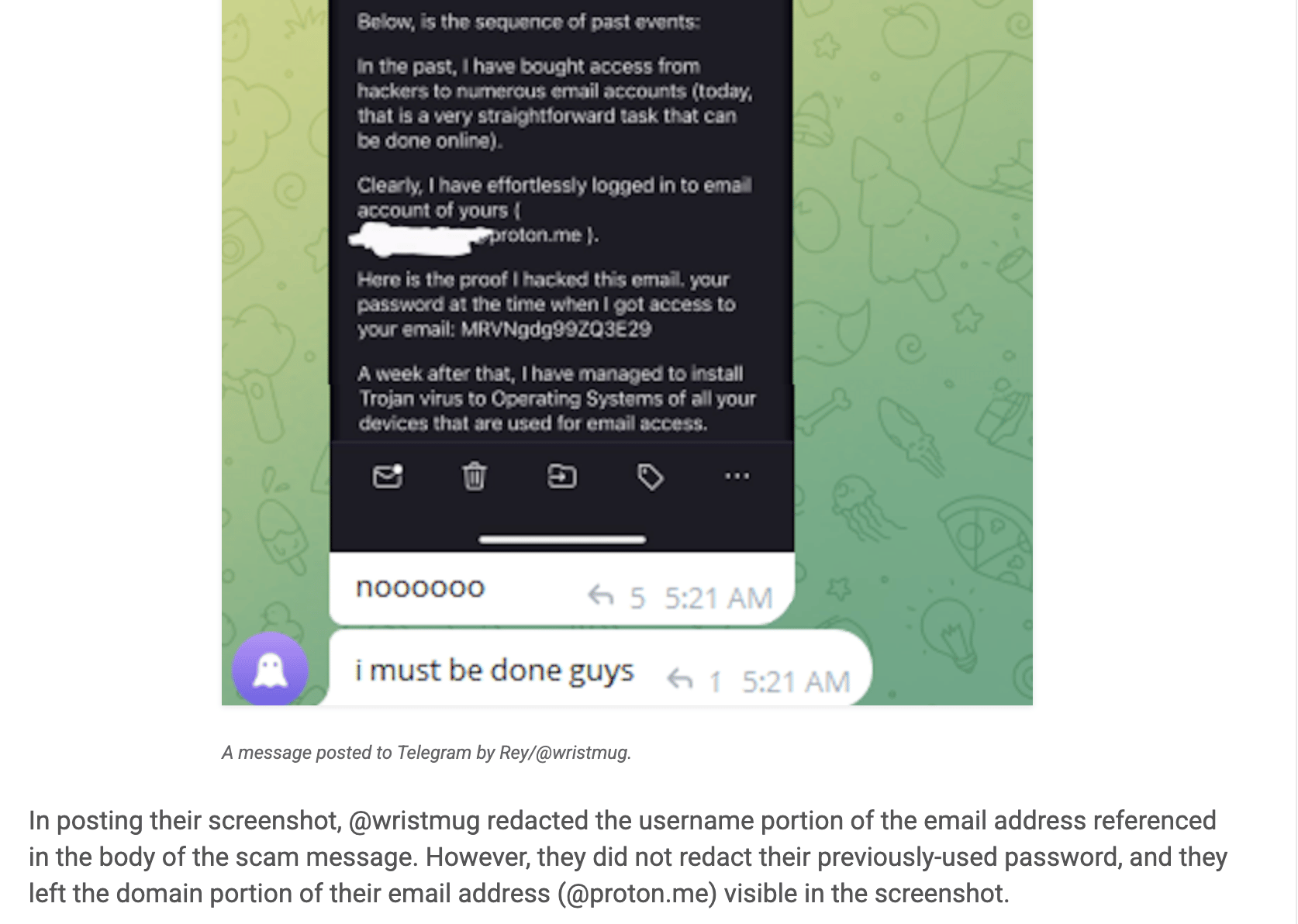
Rey's password was linked to an email that connected to previous usernames, website defacements with pro-Palestinian messages, and even family details lifted by infostealer malware on their shared PC. The kid claims he's already cooperating with European law enforcement and wants out of the game, but given that his group just launched their own ransomware-as-a-service called ShinySp1d3r, the timing seems a bit convenient. (read more)

The FBI's throwing up another warning about account takeover scams, this time focused on crooks impersonating bank support staff. Since January, they've logged over 5,100 complaints with losses north of $262 million. The playbook's pretty standard - either social engineering victims into handing over their login creds (including MFA codes), or setting up convincing phishing sites that look exactly like your bank's website. Some are even buying ads to make their fake sites show up first in Google searches.
Holiday season's ramping up the threat level too. Security firms are tracking 750 malicious holiday-themed domains popping up in just three months, plus 1.57 million stolen e-commerce credentials floating around dark web markets. Mobile phishing has jumped 4x, and there's this whole new "purchase scam" trend where fake online stores steal your payment info while you think you're buying actual products. (read more)
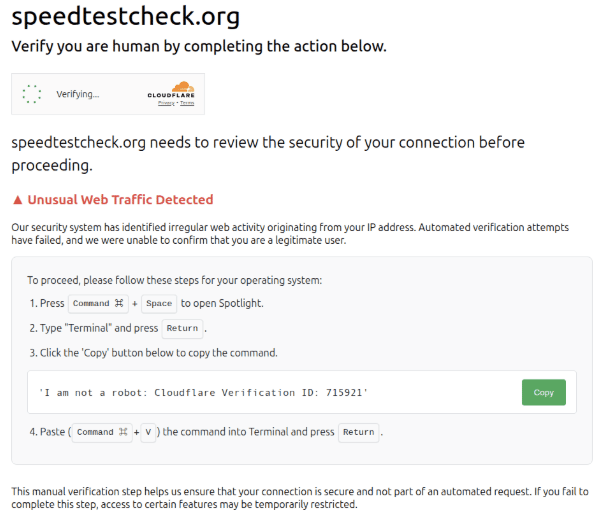
A global data storage company got hit with Akira ransomware after an employee clicked a fake CAPTCHA on a compromised car dealership site. Employee thought they were proving they weren't a bot, but instead downloaded SectopRAT malware that gave Howling Scorpius (the Akira ransomware crew) their initial foothold. The attackers then had over six weeks to wander around, compromise domain admins, and stage nearly 1TB of data for exfiltration before dropping their payload across three separate networks.
The victim had two enterprise-grade EDR solutions that were dutifully logging every single malicious action, but generated almost zero alerts. All the evidence was sitting right there in the logs, but nobody knew to look. Unit 42 found this pattern in 75% of their cases - security tools collecting data but not actually catching threats. (read more)
Crisis24 just shut down permanently(?!) on their OnSolve CodeRED emergency notification system after getting hit by ransomware earlier this month. The service was used by dozens of law enforcement agencies and municipalities for emergency alerts, and it's been down for about two weeks now. INC ransomware claimed responsibility and managed to steal user PII including names, addresses, emails, phone numbers, and passwords before leaking it all online.
The company's basically telling everyone "oops, our bad" while hustling customers over to their new CodeRED platform that they claim wasn't touched by the attack. Nice timing that they were already building a replacement, right? Some agencies like Douglas County Sheriff's Office in Colorado aren't having it and terminated their contracts immediately. (read more)
Three London councils are dealing with a cyberattack that's forced them to shut down networks and phone lines. Kensington & Chelsea, Westminster (who share IT systems), and Hammersmith & Fulham are all affected, which means public services like housing, social services, and rubbish collection are getting disrupted. They've activated emergency plans and are working with UK law enforcement on the investigation.
The councils aren't saying what kind of attack it is or who's behind it, though they claim the cause is "established" - whatever that means. They're still figuring out if any data got stolen, which is always the million-pound question in these situations. Not great timing for residents who need those services, but at least they seem to be taking the response seriously by shutting things down rather than letting attackers potentially dig deeper. (read more)
Congress is finally putting some teeth into AI-enabled fraud enforcement with the new AI Fraud Deterrence Act. The bipartisan bill jacks up penalties significantly - $1-2M fines and 20-30 year prison sentences for using AI in fraud schemes. Impersonating government officials with AI could land you a $1M fine and 3 years behind bars.
White House Chief of Staff Susie Wiles had her voice cloned for scam calls to VIPs, Secretary Rubio got deepfaked promising to cut Ukraine's Starlink access, and even the Biden campaign got hit with AI-generated robocalls in NH. While the bill won't stop determined nation-state actors, it at least gives prosecutors more leverage against domestic fraudsters getting creative with AI tools. (read more)
Miscellaneous mattjay
How'd I do this edition?It's hard doing this in a vacuum. Screaming into a void. Feedback is incredibly valuable to make sure I'm making a newsletter you love getting every week. |
Parting Thoughts:
Community was foundational in launching and propelling my career. Community is the only reason I can stand being in Texas during the summer months. Community is the point. Today, I invite you to embrace discomfort on the road to a more vulnerable you.
Stay safe, Matt Johansen
@mattjay
